What’s the worst part about packaging up a whole lot of the same basic thing? It might just be applying the various warning stickers to the outside of the shipping box. Luckily, [Mr Innovative] has built an open-source automatic sticker dispenser that does the peeling for you, while advancing the roll one at a time quite satisfyingly.
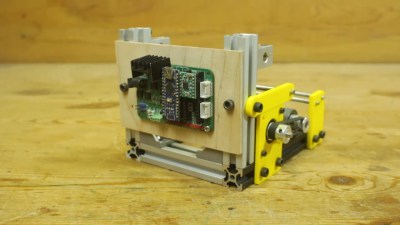 This tidy build is made primarily of 20×20 extruded aluminium and stainless steel smooth rod. All the yellow bits are 3D printed. The brains of this operation is an Arduino Nano, with an A4988 stepper motor driver controlling a NEMA17.
This tidy build is made primarily of 20×20 extruded aluminium and stainless steel smooth rod. All the yellow bits are 3D printed. The brains of this operation is an Arduino Nano, with an A4988 stepper motor driver controlling a NEMA17.
Our favorite part of this build is the IR sensor pair arranged below the ready sticker. It detects when a sticker is removed, then the stepper advances the roll by one sticker height. The waste is collected on a spool underneath.
Between the video and the instructions, [Mr Innovative] has made it quite simple to build one for yourself. Definitely check this one out after the break.
[Mr Innovative] may as well go by [Mr. Automation]. Check out this automated wire prep machine from a few years ago.