At first we thought that [Brandon Dunson] was writing in to tell us he’s too lazy to fix his bathroom fan. What he really meant is that simply replacing the unit isn’t nearly enough fun. Instead, he developed his own bathroom fan trigger based on stinky or humid air conditions. He didn’t publish a post about the project but we’ve got his entire gallery of build images after the break.
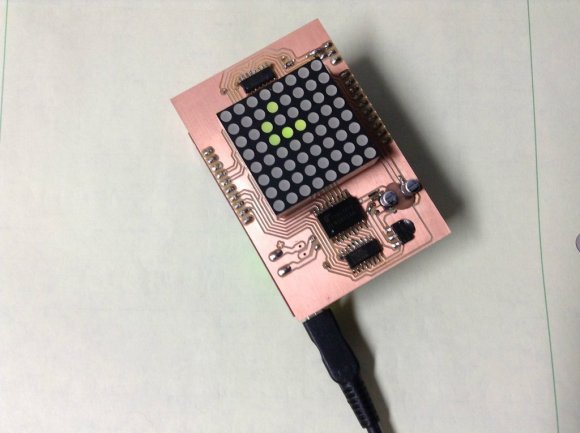
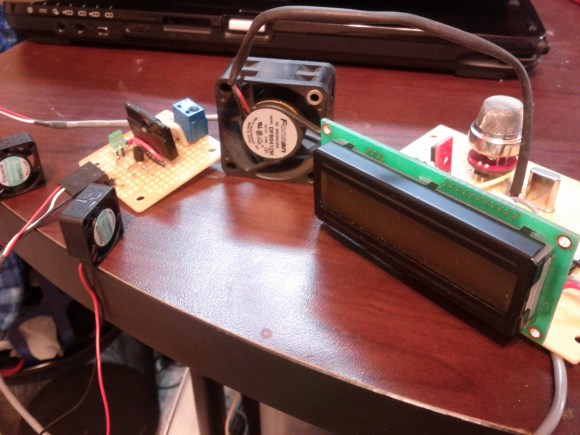
The initial inspiration for the project came from a twitter-connected fart sensing office chair. Hiding behind the character display you can see the MQ-4 methane gas sensor which he picked up for the project. But since there’s also a shower in the bathroom he included a humidity sensor with the project. Both are monitored by an ATmega328 which averages 10 readings from each sensor before comparing the data with a set threshold. If the sensors read above this level a relay turns on the bathroom fan.
Don’t be confused by the small DC fans seen above; [Brandon] is still using a proper exhaust fan. These are just used to help circulate the air around the sensors so that low-hanging smells will still trigger the system. This has got to be the perfect thing for a heavily used restroom.
Continue reading “Bathroom Fan That Switches Itself On When It Gets Steamy Or Smelly”