With the release of Smash Ultimate fast approaching for the Nintendo Switch, [Patrick Hess] wanted to get ahead of the game and make sure his squad had the equipment they’d need. Namely, support for the GameCube controllers that serious Smash Bros players demand. But it wasn’t enough to have one or two of them hooked up, or even four. Not even six GameCube controllers could satiate his desire. No, he needed to have support for eight simultaneous GameCube controllers, and he wanted to look good doing it too.
 Enter his meticulously designed eight player GameCube to USB adapter. Made out of dual official Nintendo GameCube to USB adapters (intended for the Wii U) merged together in a 3D printed case, the final result looks like something that could earn the coveted Nintendo Seal of Approval. Or at least, something that might pop up on the import sites in the next month or two for a few bucks.
Enter his meticulously designed eight player GameCube to USB adapter. Made out of dual official Nintendo GameCube to USB adapters (intended for the Wii U) merged together in a 3D printed case, the final result looks like something that could earn the coveted Nintendo Seal of Approval. Or at least, something that might pop up on the import sites in the next month or two for a few bucks.
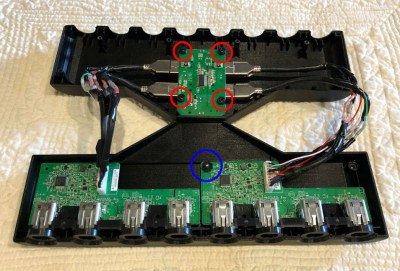
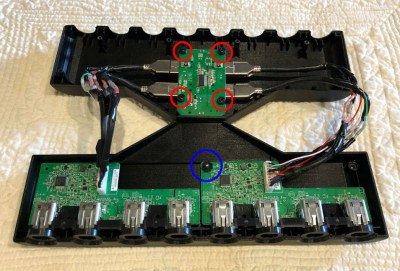
[Patrick] started the project by recreating the official adapter PCBs and their housings in 3D using a pair of calipers. After a couple of test prints to make sure he had all the dimensions right, he could then move on to designing his final enclosure knowing he had accurate data to model around.
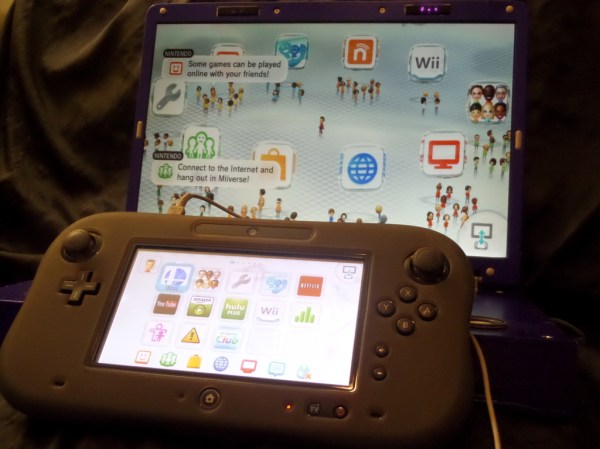
In addition to the two adapter boards, there’s also a four port USB hub inside the device’s case. Each adapter has two USB leads, here shortened to fit inside the case, which connect up to the hub. The integrated hub allows connecting all eight GameCube controllers through only a single USB connection. All controllers worked as expected during intense testing on the Wii U’s version of Smash Bros, though at this point [Patrick] can only assume it will work when the Switch version is released.
If there’s a downside to this project, it’s that the design for the 3D printed case is so intricate that [Patrick] was only able to print it on a machine that supported water-soluble PVA supports. A somewhat tall order for the average hacker; it would be interesting to see if somebody could make a second pass on the enclosure that is geared more towards printability than aesthetics.
While the design of the GameCube controller remains somewhat controversial after all these years, there’s no denying it retains an impressive following. Whether turning them into USB devices, shrinking them to preposterously small dimensions, or just finding increasingly creative ways to use them on Nintendo’s latest console, hackers are definitely in love with the gonzo little controller that’s now pushing 20 years old.