A frequent complaint you will hear about amateur radio is that it is a chequebook pursuit. Of course you can work the incredible DX if you spend $20k on a high-end radio, big antenna, and associated components. The reality is though that because it’s such a multi-faceted world there are many ways into it of which the operator with the shiny rig is taking only one.
On the commonly used HF and VHF bands at the lower end of the radio spectrum you will definitely find chequebook amateurs of the type described in the previous paragraph. But as you ascend into the microwave bands there are no shiny new radios on the market, so even the well-heeled licensee must plow their own furrow and build their own station.
You might think that this would remain a chequebook operation of a different type, as exotic microwave devices are not always cheap. But in fact these bands have a long history of extremely inexpensive construction, in which skilled design and construction as well as clever re-use of components from satellite TV systems and Doppler radar modules play a part. And it is a project following this path that is our subject today, for [Peter Knol, PA1SDB] has repurposed a modern Doppler radar module as a transmitter for the 10GHz or 3cm amateur band (Google Translate version of Dutch original). The best bit about [Peter]’s project is the price: these modules can be had for only three Euros.
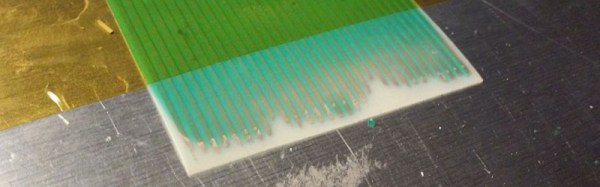
Years ago a Doppler module would have used a Gunn diode in a waveguide cavity and small horn, usually with an adjacent mixer diode for receiving. Its modern equivalent uses a transistor oscillator on a PCB, with a dielectric resonator and a set of patch antennas. There is also a simple receiver on board, but since [Peter] is using a converted ten-Euro satellite LNB for that task, it is redundant.
He takes us through the process of adjusting the module’s frequency before showing us how to mount it at the prime focus of a parabolic antenna. FM modulation comes via a very old-fashioned transformer in the power feed. He then looks at fitting an SMA connector and using it for more advanced antenna set-ups, before experimenting with the attenuating properties of different substances. All in all this is a fascinating read if you are interested in simple microwave construction.
The result is not the most accomplished 10 GHz station in the world, but it performs adequately for its extremely low price given that he’s logged a 32 km contact with it.
Though we cover our fair share of amateur radio stories here at Hackaday it’s fair to say we haven’t seen many in the microwave bands. If however you think we’ve been remiss in this area, may we point you to our recent coverage of a microwave radio receiver made from diamond?
Via Southgate ARC.