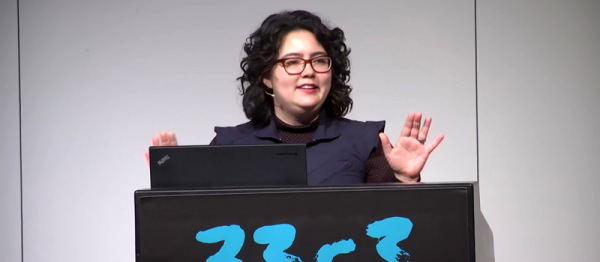
Certainly one of the more entertaining talks of the 33rd Chaos Communications Congress was [Kari Love]’s talk on her experiments in mixing food with function. In [Kari]’s talk at the 2016 Hackaday Supercon, she talked extensively about working on soft robotic for NASA. At the 33C3, her focus was twofold: on a fun side project to make mobile robots out of stuff that you can eat, and to examine the process of creative engineering through the lens of a project like this.
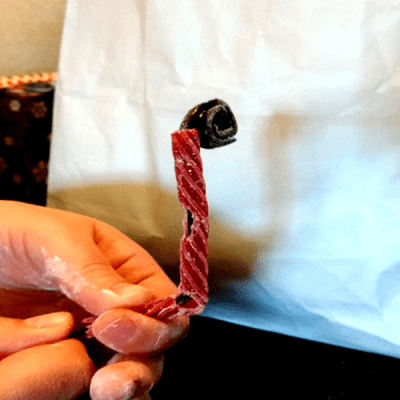
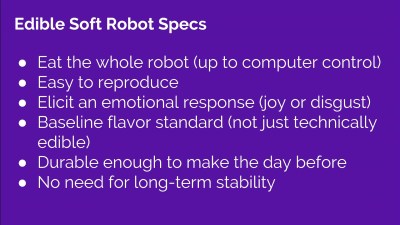
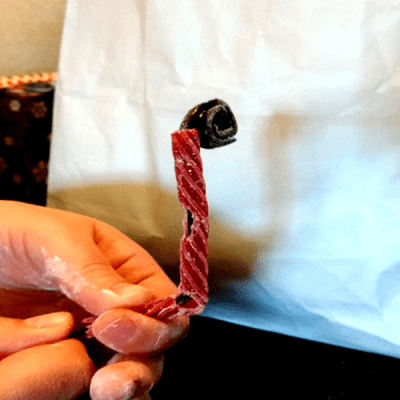
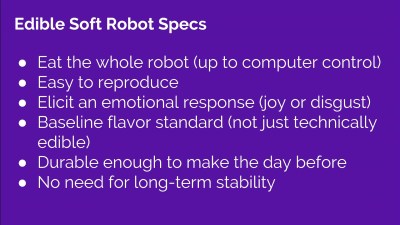 If you look up edible robotics, you get a lot of medical literature about endoscopes that you can swallow, or devices that take samples while they’re inside you. That’s not what [Kari]’s after at all. She’s after a robot that’s made of candy, a yummy machine. And while this is still a work in progress, she demonstrated a video of an all-licorice cable-based actuator.
If you look up edible robotics, you get a lot of medical literature about endoscopes that you can swallow, or devices that take samples while they’re inside you. That’s not what [Kari]’s after at all. She’s after a robot that’s made of candy, a yummy machine. And while this is still a work in progress, she demonstrated a video of an all-licorice cable-based actuator.
 But more than that, she demonstrated all of the materials she’s looked at so far, and the research she’s done. To some extent, the process is the substance of this project, but there’s nothing wrong with some tasty revelations along the way.
But more than that, she demonstrated all of the materials she’s looked at so far, and the research she’s done. To some extent, the process is the substance of this project, but there’s nothing wrong with some tasty revelations along the way.
This talk was a potpourri of helpful tips and novel facts. For instance, if you’re working in candy robotics, don’t eat your mistakes. That stomach ache that your mom always said you’d get? You will. Did you know that the gummi in gummibears is re-heatable and re-moldable? In addition, of the gels that she made, it was the most delicious. And finally, Pop Rocks don’t have enough CO2 in them to drive pneumatics. Who knew? [Kari] knows. And now you do too.
Continue reading “33C3: Edible Soft Robotics” →



 But more than that, she demonstrated all of the materials she’s looked at so far, and the research she’s done. To some extent, the process is the substance of this project, but there’s nothing wrong with some tasty revelations along the way.
But more than that, she demonstrated all of the materials she’s looked at so far, and the research she’s done. To some extent, the process is the substance of this project, but there’s nothing wrong with some tasty revelations along the way.