I was looking over the week’s posts on Hackaday – it’s part of my job after all – and this gem caught my eye: a post about how to make your own RP2040 development board from scratch. And I’ll admit that my first thought was “why would you ever want to do that?” (Not a very Hackaday-appropriate question, honestly.) The end result will certainly cost more than just buying a Pi Pico off the shelf!
Then it hit me: this isn’t a project per se, but rather [Kai] was using it as an test run to learn the PCB-production toolchain. And for that, replicating a Pico board is perfect, because the schematics are easily available. While I definitely think that a project like this is a bit complicated for a first PCB project – I’d recommend making something fun like an SAO – the advantage of making something slightly more involved is that you run into all of the accompanying problems learning experiences. What a marvelous post-complete-beginner finger exercise!
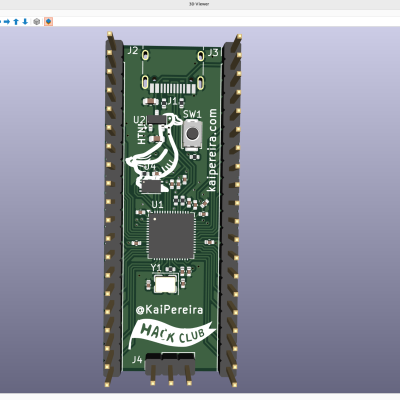 And then it hit me again. [Kai]’s documentation of everything learned during the project was absolutely brilliant. It’s part KiCAD tutorial, part journal about all the hurdles of getting a PCB made, and just chock-full of helpful tips along the way. The quality of the write-up turns it from being just a personal project into something that can help other people who are in exactly the same boat, and I’m guessing that’s a number of you out there.
And then it hit me again. [Kai]’s documentation of everything learned during the project was absolutely brilliant. It’s part KiCAD tutorial, part journal about all the hurdles of getting a PCB made, and just chock-full of helpful tips along the way. The quality of the write-up turns it from being just a personal project into something that can help other people who are in exactly the same boat, and I’m guessing that’s a number of you out there.
In the end, this was a perfect Hackaday project. Yes, it was “too simple” for those who have made their 30th PCB design. (Although I’d bet you could still pick up a KiCAD tip or two.) And yes, it doesn’t make economic sense to replicate mass-market devices in one-off. And of course, it doesn’t need that fun art on the board either. But wrap all these up together, and you get a superbly documented guide to a useful project that would walk you through 95% of what you’ll need to make more elaborate projects later on. Superb!
Surely you do “finger exercises” too. Why not write them up, and share the learning? And send them our way – we know just the audience who will want to read it.