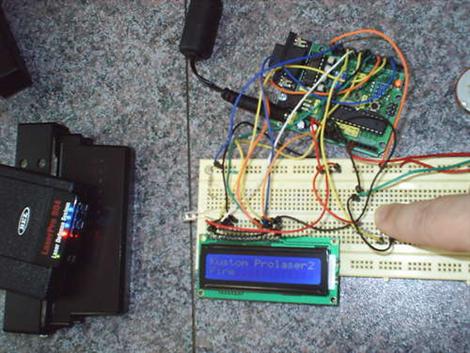
[Blacklight99] made this cool tool. It is a tester for those radar detectors that people keep in their cars. Though this seems like it would rarely be a tool we would need, it’s an interesting project. Some speed guns that the police use have a “stealth” mode that makes them invisible to some detectors. This tool can tell you if your detector is vulnerable to this. While this really is just a complicated flashing LED, he notes that it could be taken further to be made into a detector that is programmable and not vulnerable to any of the stealth modes.
LED Hacks1935 Articles
Raid The Dollar Store For An Illuminated Umbrella

Here’s a quick and easy illuminated umbrella that [Mikeasaurus] built. How’s this for economical? He found an umbrella that someone left on the bus, and used an LED flashlight and clear poncho from the dollar store for the rest of the parts.
The scavenged LED circuit board is the perfect diameter to fit inside the handle of his umbrella. He removed the middle LED and drilled a hole in the board for the shaft to pass through. Although not well detailed, we gather he managed to shoehorn two CR2032 3v batteries underneath the PCB to power the device. The poncho is wrapped around the shaft to diffuse the light. This is a clever solution as the flexible plastic still allows the telescoping shaft to collapse down to its most compact size.
[Mikasaurus’] umbrella doesn’t make noise or emulate the weather but it is a clever idea. The low difficulty level and availability of parts makes this a great project to do with the young ones who don’t get included in your more intricate hacks.
Bike Brake Light Senses You Slowing Down

Group riding can be a bit dangerous if the pace is fast and riders don’t notice a slowing in the front of the pack. [WyoJustin] designed a brake light system for cyclists to try and remedy this issue. LEDs are mounted in the end caps of the handlebars on a road bike. When an accelerometer senses the bike slowing down the LEDs light up, warning those behind you that you’re slowing down.
The system is made to be portable, as a lot of serious riders have multiple bikes. To make this happen, all of the electronics are housed in the handlebar tubing for easy transfer. This includes an accelerometer with built in voltage regulator, an Arduino to control everything, and a battery. Take a look at the brake lights in action after the break.
Most of the bike lights we see are for the front of the machine, but this backward-facing package is a clean and easy solution we can get behind (safely).
Electronic Jewelry

[Ellindsey000] posted this neat little pendant to his flickr stream. We like the way it looks, and the fact that it is a functional circuit. The schematic is even pretty neat. We would maybe wear this, as a belt buckle or something. When we looked at this though, we thought it looked really familiar. Yeah, it kind of looks like the arc reactor from Iron Man, but what we thought of was this cool looking walker. As you could probably already tell, it’s the same person. Great job again [Ellindsey000], and thanks for posting the schemtaic.
Unreasonably Bright Bike Light Apparently Hunts Deer

[Jukka] wanted a bike light that wasn’t afraid to go into the woods during the dark winter. He put together a lamp that uses eight 3 Watt LEDs to pump out 1680 lumens (english translation). The high power LEDs were mounted on a large aluminum heat sink and use lenses to optimize the beam of light. The system uses a 2 amp driver board that he assembled himself. Power is provided by sixteen AA Nickel Metal Hydride batteries that are housed along with the driver circuit in a water bottle.
This more than doubles the output of the last bike light we thought was too bright. Where will this lumen-arms-race stop?
[Thanks Sami]
War Monument Hacking

[Timo] tipped us off about a War Monument that has been… upgraded. The story starts when a monument was erected in Cherkassy, Ukraine to commemorate the ultimate sacrifice that was made by Russian soldiers during World War II. The huge statue and expansive plaza were capped off by an eternal flame. Unfortunately, when the Soviet Block broke up, the natural gas that had been provided by the government became a luxury so the flame was extinguished.
The eternal flame sat unlit, a sad commentary to the remembrance of the dead. But how to fix this issue? As cell phone companies came into the area, a need for cell phone towers arose. At some point a solution was reached; a cell phone tower was built in the bowl of the eternal flame and then wrapped with an LED marquee. The marquee now displays the image of a flame in perpetuity.
We’re not quite sure what to think about this. After some adjustment, the substitution of LEDs for flames will probably become accepted. The monument is now providing a useful purpose for the living, and once again shows a flame. We think that having something there showing that the memory is still alive is much better than the message an unkempt derelict sends.