Fail2ban is a great tool for dynamically blocking IP addresses that show bad behavior, like making repeated login attempts. It was just announced that a vulnerability could allow an attacker to take over a machine by being blocked by Fail2ban. The problem is in the mail-whois action, where an email is sent to the administrator containing the whois information. Whois information is potentially attacker controlled data, and Fail2ban doesn’t properly sterilize the input before piping it into the mail binary. Mailutils has a feature that uses the tilde key as an escape sequence, allowing commands to be run while composing a message. Fail2ban doesn’t sanitize those tilde commands, so malicious whois data can trivially run commands on the system. Whois is one of the old-school unix protocols that runs in the clear, so a MItM attack makes this particularly easy. If you use Fail2ban, make sure to update to 0.10.7 or 0.11.3, or purge any use of mail-whois from your active configs. Continue reading “This Week In Security: Fail2RCE, TPM Sniffing, Fishy Leaks, And Decompiling”
Security Hacks1571 Articles
This Week In Security: NSO, Print Spooler, And A Mysterious Decryptor
The NSO Group has been in the news again recently, with multiple stories reporting on their Pegasus spyware product. The research and reporting spearheaded by Amnesty International is collectively known as “The Pegasus project”. This project made waves on the 18th, when multiple news outlets reported on a list of 50,000 phone numbers that are reported as “potential surveillance targets.” There are plenty of interesting people to be found on this list, like 14 heads of state and many journalists.
There are plenty of questions, too. Like what exactly is this list, and where did it come from? Amnesty international has pointed out that it is not a list of people actively being targeted. They’ve reported that of the devices associated with an entry on the list that they have been able to check, roughly 50% have shown signs of Pegasus spyware. The Guardian was part of the initial coordinated release, and has some impressive non-details to add:
The presence of a phone number in the data does not reveal whether a device was infected with Pegasus or subject to an attempted hack. However, the consortium believes the data is indicative of the potential targets NSO’s government clients identified in advance of possible surveillance attempts.
Amazon’s AWS was named as part of the C&C structure of Pegasus, and in response, they have pulled the plug on accounts linked to NSO. For their part, NSO denies the validity of the list altogether. Continue reading “This Week In Security: NSO, Print Spooler, And A Mysterious Decryptor”
This Week In Security: REvil Goes Dark, Kaseya Cleanup, Android Updates, And Terrible Firmware
The funniest thing happened to REvil this week. Their online presence seems to have disappeared.
Their Tor sites as well as conventional sites all went down about the same time Tuesday morning, leading to speculation that they may have been hit by a law enforcement operation. This comes on the heels of a renewed push by the US for other countries, notably Russia, to crack down on ransomware groups operating within their borders. If it is a coordinated takedown, it’s likely a response to the extremely widespread 4th of July campaign launched via the Kaseya platform. Seriously, if you’re going to do something that risks ticking off Americans, don’t do it on the day we’re celebrating national pride by blowing stuff up.
All REvil sites are down, including the payment sites and data leak site. 🤔
The public ransomware gang represenative, Unknown, is strangely quiet.
— Lawrence Abrams (@LawrenceAbrams) July 13, 2021
Speaking of Kaseya, they have finished their analysis, and published a guide for safely powering on their VSA on-premise hardware. Now that the fixes are available, more information about the attack itself is being released. Truesec researchers have been following this story in real time, and even provided information about the attack back to Kaseya, based on their observations. Their analysis shows that 4 separate vulnerabilities were involved in the attack. First up is an authentication bypass. It takes advantage of code that looks something like this: Continue reading “This Week In Security: REvil Goes Dark, Kaseya Cleanup, Android Updates, And Terrible Firmware”
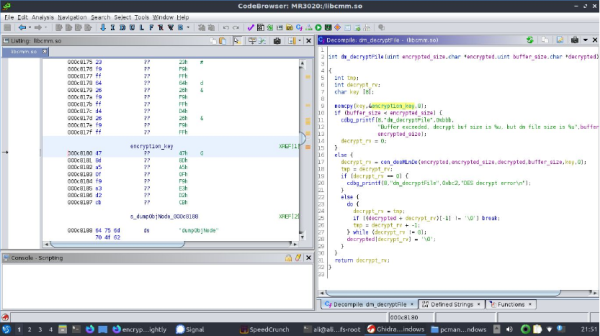
Using Ghidra To Extract A Router Configuration Encryption Key
Who doesn’t know the struggle? Buying an interesting piece of hardware for a song and a dance, and then finding that the device’s firmware and/or configuration file is locked down with various encryption or obfuscation methods. This was the experience [Ali Raheem] had when he got a TP-Link TL-MR3020 V3 for a mere 18 British Pounds, intending to use this 4G-capable router to increase internet reliability.
Naturally this can all be done when staying inside the vendor-provided marked lines, which in this case meant ignoring the encrypted configuration files. As the owner of the hardware, this was of course unacceptable and thus [Ali] got a firmware image from the TP-Link site to see what could be gleaned from it in terms of encryption keys and other hints.
After obtaining the TP-Link-provided BIN file, the application of binwalk helpfully extracted the files embedded in it, followed by John the ripper decrypting the passwords in the /etc/passwd.bak file, and ultimately finding the encrypted /etc/default_config.xml file. Searching for this filename string in the rest of the extracted files led to /lib/libcmm.so.
Dropping this shared library file into Ghidra to disassemble its code, [Ali] found a function suspiciously called decryptFile. Inside was a reference to the global key string, which when tossed into OpenSSL and after some fiddling turned out to decrypt the XML configuration file in des-ecdb mode. From this point dropping in one’s own configuration files should be no problem after encrypting them to make the firmware happy. Nice work!
NFC Who’s At The Door
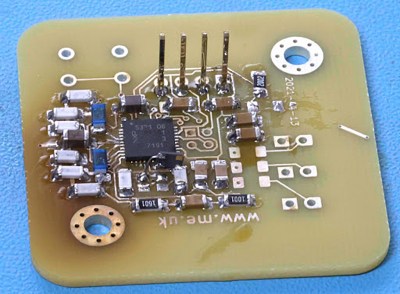
[RevK] wanted to learn about NFC readers, and we agree that the best way to do so is to dive in and build one yourself.
There are readers available from multiple sources, but [RevK] found them either compact but with no prototyping space or plenty of prototyping space and a large footprint. High-speed UART (HSU) was selected over I2C for communication with an ESP32 as testing showed it was just as fast and more reliable over long distances at the cost of only one additional wire.
After a few versions, the resulting PN532 based NFC reader has just enough GPIO for a doorbell and tamper switch and three status LEDs, with board files and a 3D-printed case design included in the open source project on GitHub. When looking into the project, we appreciated learning about tamper switches that can include closed or open contact status when an NFC is read, most often used in the packaging of high-value and collectible products. If you have worked with this tamper feature of NFCs, let us know about it.
Thanks for the tip, [Simon]
This Week In Security: Print Nightmare Continues, Ransomware Goes Bigger, And ATM Jackpots!
For the second time, Microsoft has attempted and failed to patch the PrintNightmare vulnerability. Tracked initially as CVE-2021-1675, and the second RCE as CVE-2021-34527. We warned you about this last week, but a few more details are available now. The original reporter, [Yunhai Zhang] confirms our suspicions, stating on Twitter that “it seems that they just test with the test case in my report”.
CVE-2021-1675 is meant to fix PrintNightmare, but it seems that they just test with the test case in my report, which is more elegant and also more restricted. So, the patch is incomplete. : (
— Yunhai Zhang (@_f0rgetting_) July 1, 2021
Microsoft has now shipped an out-of-band patch to address the problem, with the caveat that it’s known not to be a perfect fix, but should eliminate the RCE element of the vulnerability. Except … if the server in question has the point and print feature installed, it’s probably still vulnerable. And to make it even more interesting, Microsoft says they have already seen this vulnerability getting exploited in the wild. Continue reading “This Week In Security: Print Nightmare Continues, Ransomware Goes Bigger, And ATM Jackpots!”
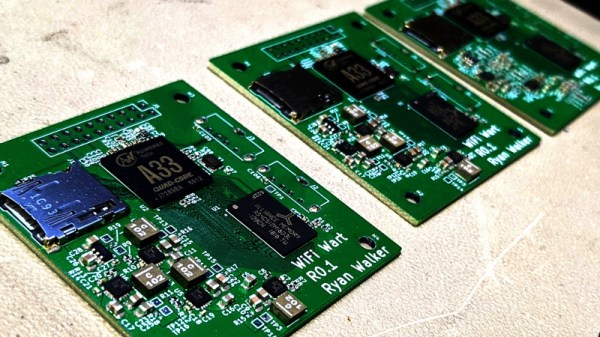
WiFiWart Linux Pentesting Device Gets First PCBs
When we last checked in on the WiFiWart, an ambitious project to scratch-build a Linux powered penetration testing drop box small enough to be disguised as a standard phone charger, it was still in the early planning phases. In fact, the whole thing was little more than an idea. But we had a hunch that [Walker] was tenacious enough see the project through to reality, and now less than two months later, we’re happy to report that not only have the first prototype PCBs been assembled, but a community of like minded individuals is being built up around this exciting open source project.
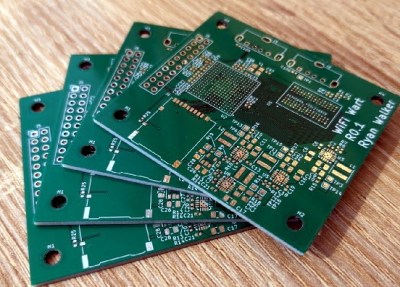 Now before you get too excited, we should probably say that the prototypes didn’t actually work. Even worse, the precious Magic Smoke was released from the board’s Allwinner A33 ARM SoC when a pin only rated for 2.75 V was inadvertently fed 3.3 V. The culprit? Somehow [Walker] says he mistakenly ordered a 3.3 V regulator even though he had the appropriate 2.5 V model down in the Bill of Materials. A bummer to be sure, but that’s what prototypes are for.
Now before you get too excited, we should probably say that the prototypes didn’t actually work. Even worse, the precious Magic Smoke was released from the board’s Allwinner A33 ARM SoC when a pin only rated for 2.75 V was inadvertently fed 3.3 V. The culprit? Somehow [Walker] says he mistakenly ordered a 3.3 V regulator even though he had the appropriate 2.5 V model down in the Bill of Materials. A bummer to be sure, but that’s what prototypes are for.
Even though [Walker] wasn’t able to fire the board up, the fact that they even got produced shows just how much progress has been made in a relatively short amount of time. A lot of thought went into how the 1 GB DDR3 RAM would get connected to the A33, which includes a brief overview of how you do automatic trace length matching in KiCad. He’s also locked in component selections, such as the RTL8188CUS WiFi module, that were still being contemplated as of our last update.
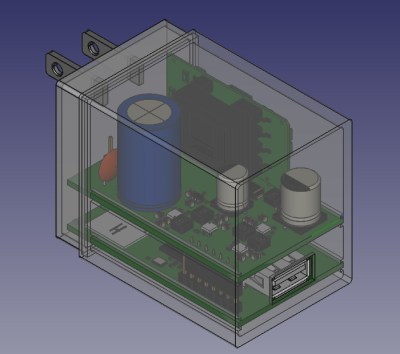
Towards the end of the post, he even discusses the ultimate layout of the board, as the one he’s currently working on is just a functional prototype and would never actually fit inside of a phone charger. It sounds like the plan is to make use of the vertical real estate within the plastic enclosure of the charger, rather than trying to cram everything into a two dimensional design.
Want to get in on the fun, or just stay updated as [Walker] embarks on this epic journey? Perhaps you’d be interested in joining the recently formed Open Source Security Hardware Discord server he’s spun up. Whether you’ve got input on the design, or just want to hang out and watch the WiFiWart get developed, we’re sure he’d be happy to have you stop by.
The first post about this project got quite a response from Hackaday readers, and for good reason. While many in the hacking and making scene only have a passing interest in the security side of things, we all love our little little Linux boards. Especially ones that are being developed in the open.