It’s April, which means all the people responsible for doubling the number of badges at DEF CON are hard at work getting their prototypes ready and trying to fund the entire thing. The first one out of the gate is Da Bomb, by [netik] and his crew. This is the same team that brought you the Ides of DEF CON badge, a blinky wearable multiplayer game that’s SPQR AF. Da Bomb is now a Kickstarter campaign to get the funding for the run of 500, and you’re getting a wearable badge filled with puzzles, Easter eggs, and a radio-based sea battle game that obviously can’t be called Battleship, because the navy doesn’t have battleships anymore.
Speaking of badges and various badge paraphernalia, there’s a new standard for add-ons this year. The Shitty Add-On V.1.69bis standard adds two pins and a very secure shrouded connector that solves all the problems of last year’s standard. [AND!XOR] just released a Shitty Brooch that powers all Shitty Add-Ons with a CR2032 battery. All the files are up on the Gits, so have fun.
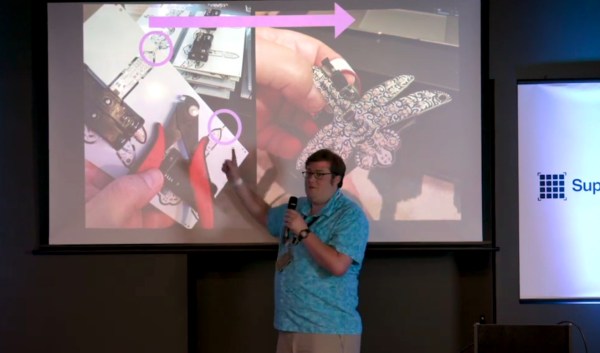
You can 3D print anything if you don’t mind dealing with supports. But how to remove supports? For that [CCecil] has a great tip: use Chap stick. This is a print that used supports and it’s perfectly clean, right off the bed. By inserting a suspend (M600) command at the z-height of the top of the interface layer, then adding Chap stick on the top layer, everything comes off clean. Neat.
Speaking of 3D printing, here’s a project for anyone with the patience to do some serious modeling. It’s a pocket Soviet record player, although I think it’s more properly called a gramophone. It’s crank powered, so there’s a spring in there somewhere, and it’s entirely acoustic with zero electronics. Yes, you’re going to need a needle, but I’d be very interested in seeing somebody remake this using modern tools and construction materials.