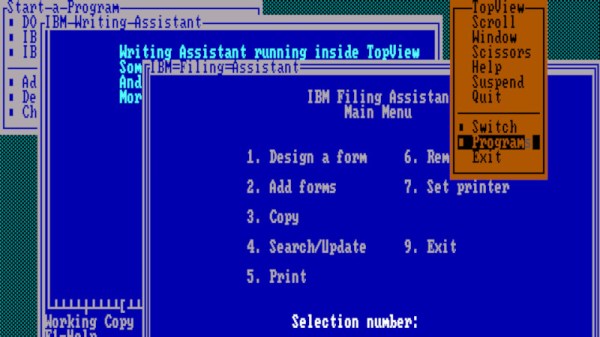
It might seem like the days of MS-DOS were a lifetime ago because…well, they basically were. Version 6.22 of the venerable operating system, the last standalone release, came out back in 1994. That makes even the most recent version officially 30 years old. A lot has changed in the computing world since that time, so naturally trying to run such an ancient OS on even a half-way modern machine would be a waste of time. Right?
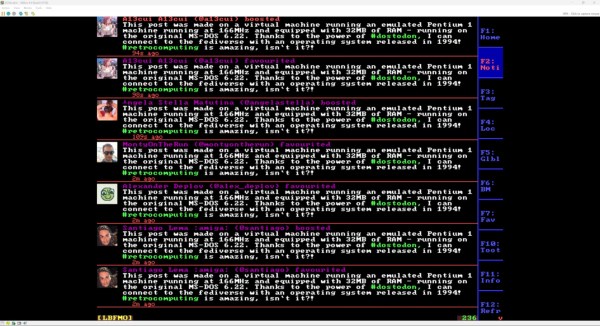
As it turns out, getting MS-DOS 6.22 running on a modern computer isn’t nearly as hard as you’d think. In fact, it works pretty much perfectly. Assuming, that is, you pick the right machine. [Yeo Kheng Meng] recently wrote in to share his experiments with running the final DOS release on his Intel-powered ThinkPad X13 from 2020, and the results are surprising to say the least.
To be clear, we’re not talking about some patched version of DOS here. There’s no emulator at work either. Granted [Yeo] did embrace a few modern conveniences, such as using a USB floppy drive emulator to load the disk images instead of fiddling with actual floppies, and installing DOS onto an external drive so as not to clobber his actual OS on the internal NVME drive. But other than that, the installation of DOS on the ThinkPad went along just as it would have in the 1990s.
Continue reading “Running Stock MS-DOS On A Modern ThinkPad”