If you wanted to host a website, you could use any one of a number of online services, or spin up a server on a spare computer at home. If you’re a bit more daring, you could also do what [Tech1k] did, and run one on an ESP32 microcontroller.
The site in question is available (or at least, should be) at HelloESP.com. The first revision ran entirely on an ESP32, serving pages from a SPIFFS filesystem. The device was also fitted with a BME280 environment sensor and an OLED screen. It had an uptime of 500 days before the board failed.
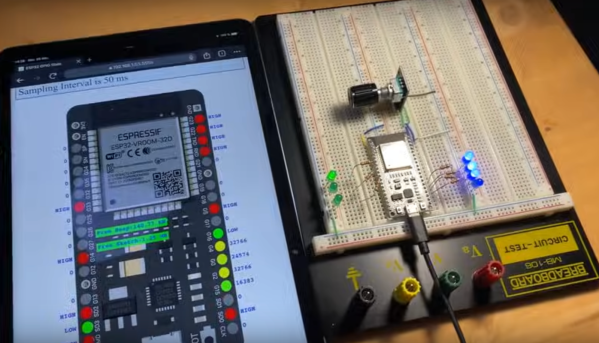
The site has since been relaunched, running on a board that is framed on [Tech1k]’s wall. It runs on an ESP32-WROOM-32D, paired with a BME280 again, along with a CCS811 CO2 and air quality sensor and a DS3231 RTC for accurate timekeeping. The ESP32 is setup to hold an outbound WebSocket to a Cloudflare worker, with the Worker routing HTTP requests to the site via that route. This avoids the need for port forwarding for the ESP32 to be visible to the outside world, and the Cloudflare Worker will also serve a static version of the page in the case of WiFi dropouts or other temporary failures.
It’s true that this isn’t a completely unheard of project—microcontrollers have been working as simple web servers for a long time now. Still, [Tech1k] did a great job of making this as robust as possible and more like a real functional webserver rather than just something that runs on a local network to serve up a config page. That’s worthy of note.
You can run webservers on all kinds of chips these days, even the Raspberry Pi Pico. If you’re doing web stuff on something weird, you know we always wanna hear about it on the tipsline!