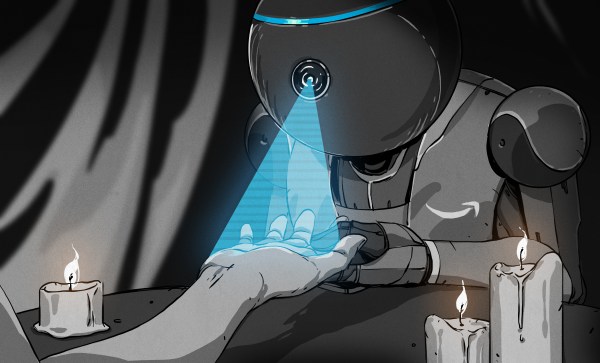
Have you heard about this One? At least three United States senators have, and they want to know what Amazon plans to do with all the biometric data collected by the Amazon One program. It’s their new contactless payment method that uses your unique palm print instead of cards or phones to make purchases, gain access to venues of work and play, and enter or pay in whatever other spaces Amazon can invade down the line. The idea is that one day, we’ll all be able to leave our homes without any form of money or ID of any kind, because we’ll all be stored away in Bezos’ big biometric file cabinet.
We tossed this one around in the writer’s room back when the Amazon One concept was nothing but a pile of buzzwords and a render or two, but these kiosks are now active in 50+ Whole Foods and Amazon 4-Star locations across the US. Here’s the deal: you can only sign up at a participating store that has a kiosk, because they have to scan your palms into the system. We were worried that the signup kiosk could easily take fingerprint scans at the same time, but according to the gifs in Morning Brew’s review, it just uses another of their point-of-sale palm scanners along with a touch screen and a card reader. But you still have to hover your entire hand over it, so who’s to say that the scan ends where the fingers begin?
Continue reading “Ask Hackaday: What Is Amazon Thinking By Entering The Palm-Reading Business?”