There are many solutions for remote control keyboards, be they Bluetooth, infrared, or whatever else. Often they leave much to be desired, and come with distinctly underwhelming physical buttons. [konkop] has a solution to these woes we’ve not seen before, turning an ESP32-S3 into a USB HID keyboard with a web interface for typing and some physical keyboard macro buttons. Instead of typing on the thing, you connect to it via WiFi using your phone, tablet, or computer, and type into a web browser. Your typing is then relayed to the USB HID interface.
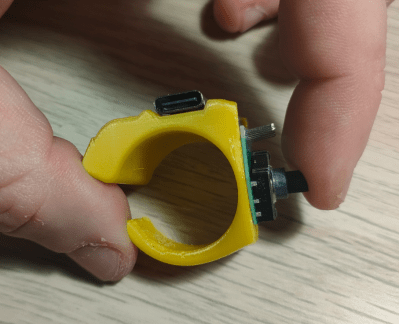
The full hardware and software for the design is in the GitHub repository. The macro buttons use Cherry MX keys, and are mapped by default to the common control sequences that most of us would find useful. The software uses Visual Studio Code, and PlatformIO.
We like this project, because it solves something we’ve all encountered at one time or another, and it does so in a novel way. Yes, typing on a smartphone screen can be just as annoying as doing so with a fiddly rubber keyboard, but at least many of us already have our smartphones to hand. Previous plug-in keyboard dongles haven’t reached this ease of use.