Computer memory is a problem that has been solved for many years. But early on, it was more than just a small problem. We’ve many of the different kinds at Hackaday over the years, and we’ll link to some of them later on. But one of the original types of memory was called Delay Line memory, which worked by waiting for a signal to propagate slow enough through a device that it was essentially stored in the device. This was highly inefficient, but still a neat concept- one that [Tom7] has taken to entirely new levels of amazing and impractical as seen in the video below the break.
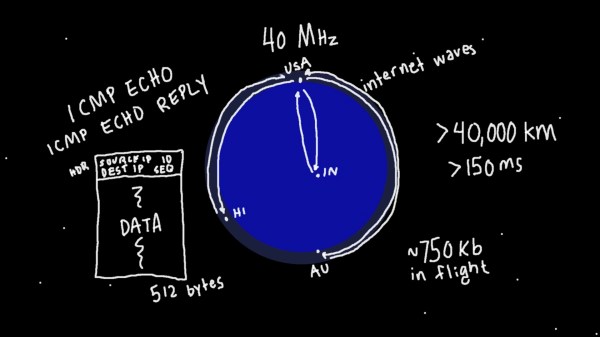
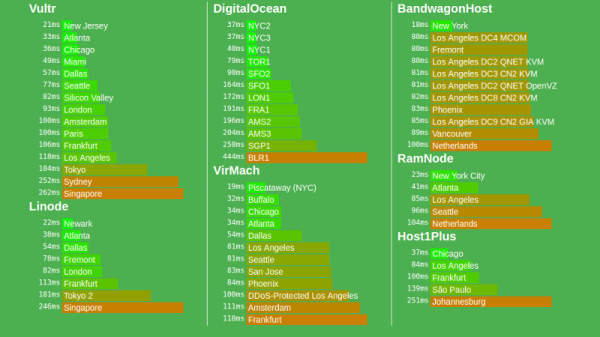
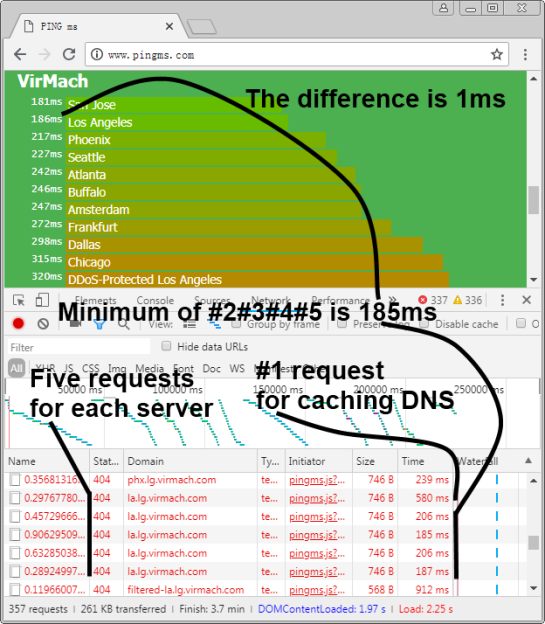
Starting with a demonstration of orbiting chainsaws, he then moves on to explaining how radio propagation waves could be used to temporarily store data while it’s in transit. He missed the opportunity to call it cloud storage, but we’ll forgive him. Extrapolating that further, he decided to use the Entire Internet to store data without its permission, utilizing large ICMP packets and even making it available as block storage in Linux.
Not content to use the entire Internet to store a few kb of data, he moved on to several thousand virtualized NES game systems which are all playing “an inventory management survival horror game” commonly known as Tetris. [Tom7] deconstructs Tetris, analyzing its Random Number Generator, gaming the system to store data in virtual NES consoles by the thousands. What data did he store? The source code to Tetris for the NES. And what did he do with it? Well, he mounted it and ran the program, of course!
The last Harder Drive we’ll leave for those who want to watch the video, because it’s a bit on the “ewww gross!” side of things but is also a bit less successful due to some magic smoke being released.
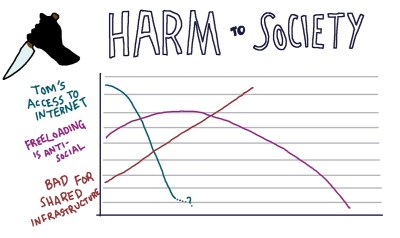
If none of these things we’ve mentioned were enough, then watch the video for an excellent breakdown of the cost, efficiency, and even the harm to society. For fun, he also tosses blockchain into the mix to see how it fares against the Harder Drives. There’s also at least one easter egg in the video, and the whimsical discussion of engineering is both entertaining and inspiring. How would you implement a Harder Drive?
[Tom7] also gives you the opportunity to follow along with the fun and mayhem by making much of the code available for your perusal. For more fun reading, check out this walk down computer memory lane that we covered last year, as well as a look into Acoustic Delay Line memory.
Continue reading “Hard(er) Drives: Impractical, Slow, Amazing, And Incredible”