Even [maurycyz] doesn’t think it is a good idea, but it is possible to use an AVR 8-bit CPU to serve web pages. Of course, it is a vastly simplified web server, but it does serve pages — OK, technically just one page — to the public Internet.
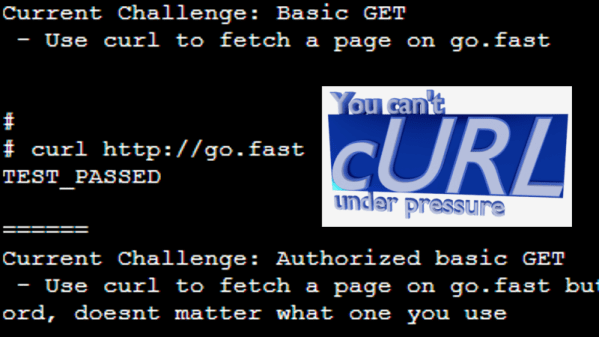
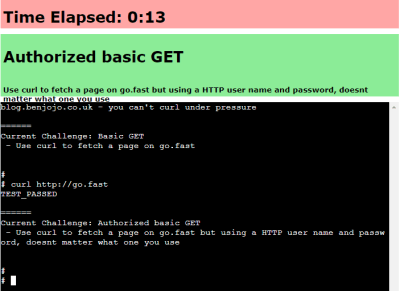
Working backward, it is fairly easy to get the microcontroller to note an HTTP request and then simply spit out a prerecorded HTTP response to provide the page. The hard part is connecting the little processor to the network. The server is dead simple, just a CPU and a scant number of components like filter caps and LEDs. The trick is to use SLIP, an ancient protocol used to connect dial-up modem terminals to the network.
Linux supports SLIP, so the MCU connects to a Linux computer via SLIP. Then the Linux computer uses WireGuard to network with the remote web server that serves [maurycyz’s] site. The SLIP implementation assumes that IP packets aren’t fragmented, which is normally true these days. TCP was a bit more complicated since you have to track the connection state and possibly re-transmit lost packets. Still, nothing the AVR with 8 K of RAM and 64 K of flash can’t handle.
Practical? No. Cool? Sort of. Funny that a disposable vape has more CPU power. Of course, something like an ESP32 is an obvious choice.