ECE 4760/5730 is the Digital Systems Design Using Microcontrollers course at Cornell University taught by [Hunter Adams]. The list of projects for spring this year includes forty write-ups — if you haven’t got time to read the whole lot you can pick a random project between 1 and 40 with: shuf -i 1-40 -n 1 and let the cards fall where they may. Or if you’re made of time you could spend a few days watching the full playlist of 119 projects, embedded below.
We won’t pick favorites from this semester’s list of projects, but having skimmed through the forty reports we can tell you that the creativity and acumen of the students really shines through. If the name [Hunter Adams] looks familiar that might be because we’ve featured his work here on Hackaday before. Earlier this year we saw his Love Letter To Embedded Systems.
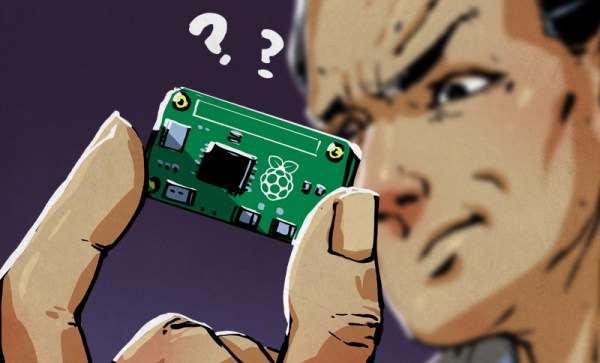
While on the subject, [Hunter] also wanted us to know that he has updated his lectures, which are here: Raspberry Pi Pico Lectures 2025. Particularly these have expanded to include a bunch of Pico W content (making Bluetooth servers, connecting to WiFi, UDP communication, etc.), and some fun lower-level stuff (the RP2040 boot sequence, how to write a bootloader), and some interesting algorithms (FFT’s, physics modeling, etc.).
Continue reading “The Latest Projects From Cornell’s ECE 4760/5730”