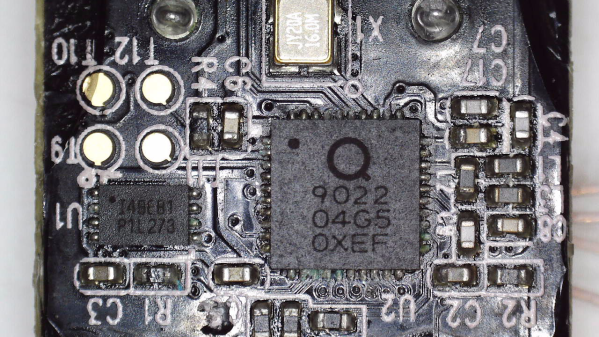
Say you’re tinkering with a smart device powered by a CPU that uses Serial Wire Debug (SWD), but doesn’t mark the testpoints. Finding SWD on a board — how hard could it be? With [Aaron Christophel]’s method, you can find the SWD interface on a PCB within a few minutes’ time. All you need is two needles, a known-to-be-ground connection, an SWD dongle of some kind, and a computer with an audio output. What’s best — you could easily transfer the gist of this method to other programming interface types!
The idea is simple: you wire the ground up, connect the needles to SWDIO and SWCLK, launch [Aaron]’s Python script, then start poking around all the unnamed test points. The script runs JLink software to probe for SWD devices attached to the probes — if an SWD interface isn’t found, it beeps idly, but as soon as the device is detected, your computer will start beeping at you in a lively manner. In this way, you don’t have to re-scan devices manually, solder to any test points except the GND one, or try and hold both probes on test points with one hand – the scanning process itself is hands-free.
Depending on how many points your board has and whether you try to optimize the process by probing points closest to the SWD pins on the CPU, you might hit the jackpot immediately, or you might have to poke around for a minute-two. That said, [Aaron]’s method seems to be the best you can do while remaining relatively extra-hardware-free, and if you want to make it a tinge more permanent, clothespins are there for you.
In case you don’t mind extra hardware – could we interest you in some 3D printed needle probe desks? There’s a wide variety of those, whether you’d like some tentacle-like ones, or ones that make your desk look like like an acupuncture table. Or, say, would you like a more automatic method of finding all kinds of debug interfaces? Then JTAGulator might be what you’re looking for.
Continue reading “Find SWD Points Quickly, No Extra Hardware Needed” →