Regular Hackaday readers will have noted a succession of stories following the reports of drones in the air over British airports and in proximity to aircraft. We’ve consistently asked for a better quality of investigation and reporting into these cases, because so far the absence of reported tangible evidence of a drone being present casts doubt on the validity of the official reaction. For too long the official records of air proximity incidents have relied upon a shockingly low standard of proof when apportioning blame to drone operators, and this situation has contributed to something of a panic over the issue.
It seems that some members of the British drone flying community are on the case though. Airprox Reality Check are a group analysing air proximity reports and linking them to contemporary ADS-B and weather records to identify possible explanations. They have devised a rating system based upon a number of different metrics in an attempt to quantify the reliability of a particular report, and they are tabulating their analysis of air proximity reports on a month by month basis. This includes among many analyses such gems as Airprox Report #2019046, in which an Embraer 170 flying at 9000 feet and 20 km offshore reported a drone in close proximity. The Airprox Reality Check analysis points out that no known drone could manage that feat, and refers to a passing Boeing 737 revealed through ADS-B data as a more likely culprit.
Their latest news is that they have made a Freedom of Information request to the Air Proximity Board, asking for what evidence the Board has of a drone having been involved in any of the over 350 incidents in UK airspace having been reported as involving drones. The official response contains the following quote:
in all cases UKAB has no confirmation that a drone has flown close to an aircraft other than the report made by the pilot(s). Similarly, other than from the report of the pilot(s), UKAB has no confirmation that a drone was involved.
This confirms the view of the multirotor and drone community that has been reported by Hackaday in the past, that the whole British drone panic has been based upon unreliable and uncorroborated reports from eyewitnesses with little direct experience of multirotors. If any irresponsible drone operator is flying into close proximity with aircraft or otherwise into protected airspace then it goes without saying that they should be prosecuted, yet it seems that the community is being punished as though this had happened when the reality is that no such acts are proven to have occurred.




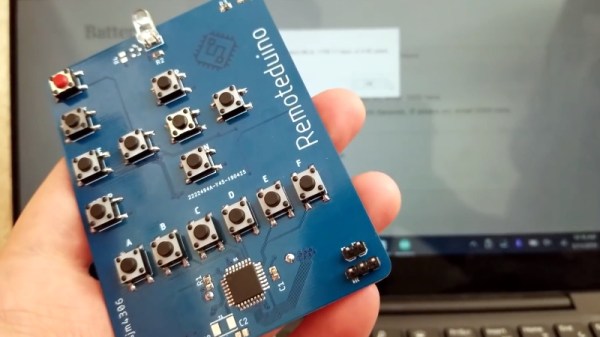
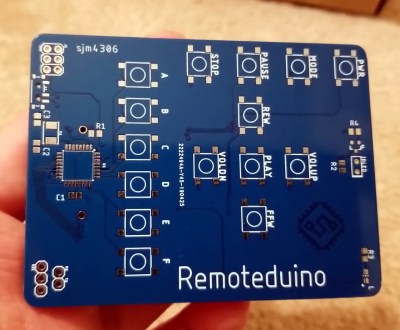
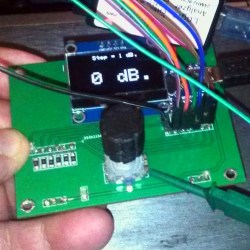 In the RF world, attenuators are a useful test and measurement tool. Variable units that can apply different levels of attenuation in discrete steps are even better. [DuWayne] made
In the RF world, attenuators are a useful test and measurement tool. Variable units that can apply different levels of attenuation in discrete steps are even better. [DuWayne] made