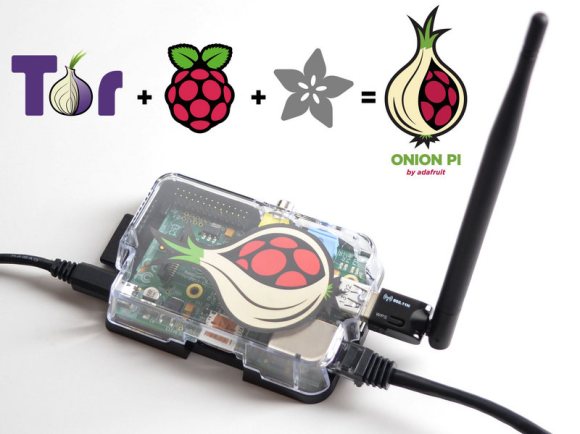
Your web traffic is being logged at many different levels. There are a few different options to re-implement your privacy (living off the grid excluded), and the Tor network has long been one of the best options. But what about when you’re away from you home setup? Adafruit has your back. They’ve posted a guide which will turn a Raspberry Pi into a portable Tor proxy.
The technique requires an Ethernet connection, but these are usually pretty easy to come by in hotels or relatives’ homes. A bit of work configuring the Linux network components will turn the RPi into a WiFi access point. Connect to it with your laptop or smartphone and you can browse like normal. The RPi will anonymize the IP address for all web traffic.
Leveraging the Tor network for privacy isn’t a new subject for us. We’ve looked at tor acks that go all the way back to the beginnings of Hackaday. The subject comes and goes but the hardware for it just keeps getting better!