Many of us have them, few of us really hack on them: well, here we’re talking about large home appliances. [Severin von Wnuck-Lipinski] and [Hajo Noerenberg] were both working on washing machines, found each other, and formed a glorious cooperation that ended in the unholy union of German super-brands Miele and B/S/H — a Miele washer remote controlled by Siemens’ web app.
This talk, given at the 39th Chaos Communication Congress (39C3), is about much more than the stunt hack, however. In fact, we covered [Severin]’s work on the very clever, but proprietary, Miele Diagnostic Interface a little while ago. But now, he’s got it fully integrated into his home automation system. It’s a great hack, and you can implement it without even opening the box.
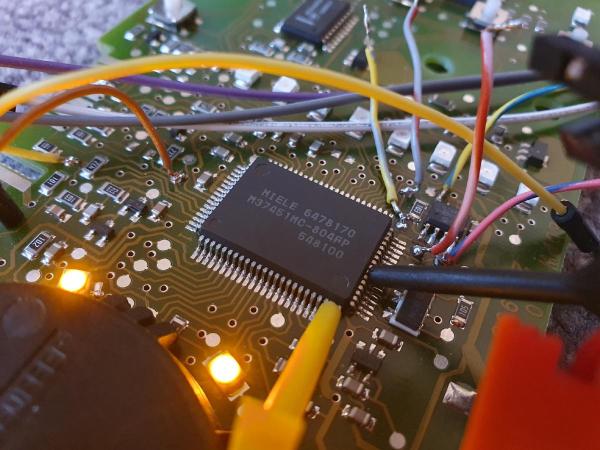
About halfway through the talk, [Hajo] takes over, dissecting the internal D-Bus communication protocol. Here, you have to open up the box, but then you get easy access to everything about the internal state of the machine. And D-Bus seems to be used in a wide range of B/S/H/ home appliances, so this overview should give you footing for your own experimentation on coffee machines or dishwashers as well. Of course, he wires up an ESP32 to the bus, and connects everything, at the lowest level, to his home automation system, but he also went the extra mile and wrote up a software stack to support it.
It’s a great talk, with equal parts humor and heroic hacking. If you’re thinking about expanding out your own home automation setup, or are even just curious about what goes on inside those machines these days, you should absolutely give it a watch.
Editor Note: The “S” is Siemens, which is Hackaday’s parent company’s parent company. Needless to say, they had nothing to do with this work or our reporting on it.