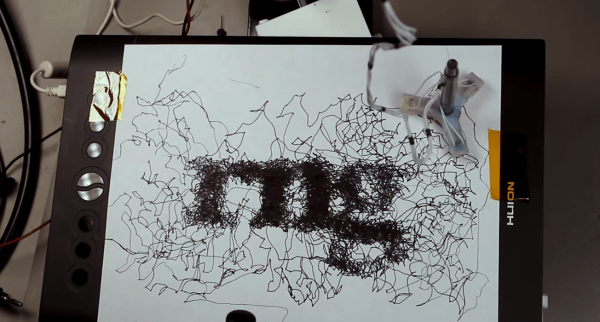
For the price of a toothbrush and a small motor with an offset weight, a bristlebot is essentially the cheapest robot that can be built. The motor shakes the toothbrush and the bristle pattern allows the robot to move, albeit in a completely random pattern. While this might not seem like a true robot that can interact with its environment in any meaningful way, [scanlime] shows just how versatile this robot – which appears to only move randomly – can actually be used to make art in non-random ways.
Instead of using a single bristlebot for the project, three of them are built into one 3D printed flexible case where each are offset by 120°, and which can hold a pen in the opening in the center. This allows them to have some control on the robot’s direction of movement. From there, custom software attempts to wrangle the randomness of the bristlebot to produce a given image. Of course, as a bristlebot it is easily subjected to the whims of its external environment such as the leveling of the table and even the small force exerted by the power/communications tether.
With some iterations of the design such as modifying the arms and control systems, she has an interesting art-producing robot that is fairly reliable for its inherently random movements. For those who want to give something like this a try, the code for running the robot and CAD files for 3D printing the parts are all available on the project’s GitHub page. If you’re looking for other bristlebot-style robots that do more than wander around a desktop, be sure to take a look at this line-following bristlebot too.
Thanks to [johnowhitaker] for the tip!




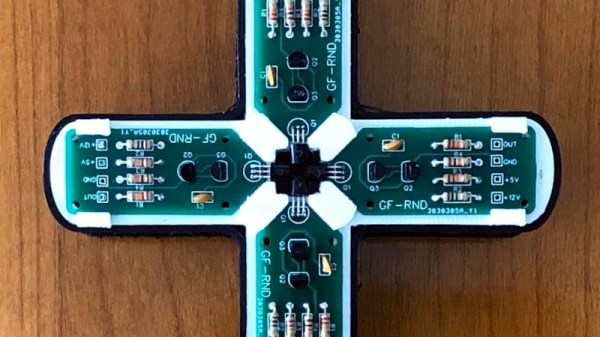
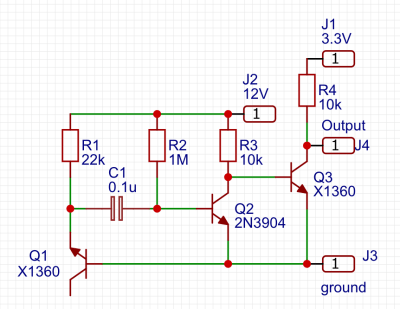 One of the simplest circuits for generating random analogue noise involves a reverse biased diode in either Zener or avalanche breakdown, and it is a variation on this that he’s using. A reverse biased emitter junction of a transistor produces noise which is amplified by another transistor and then converted to a digital on-off stream of ones and zeroes by a third. Instead of a shift register to create his four bits he’s using four identical circuits, with no clock their outputs randomly change state at will.
One of the simplest circuits for generating random analogue noise involves a reverse biased diode in either Zener or avalanche breakdown, and it is a variation on this that he’s using. A reverse biased emitter junction of a transistor produces noise which is amplified by another transistor and then converted to a digital on-off stream of ones and zeroes by a third. Instead of a shift register to create his four bits he’s using four identical circuits, with no clock their outputs randomly change state at will.










