It’s all well and good having a security camera recording all the time, but that alone can’t sound the alarm in the event of a crime. Motion sensing is of limited use, often being triggered by unimportant stimuli such as moving shadows or passing traffic. [Tegwyn☠Twmffat] wanted a better security system for the farm, and decided that neural networks would likely do the trick.
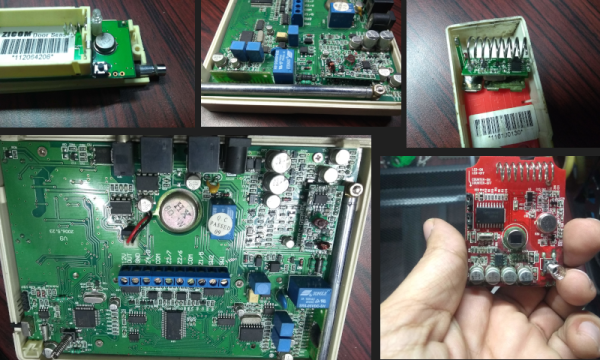
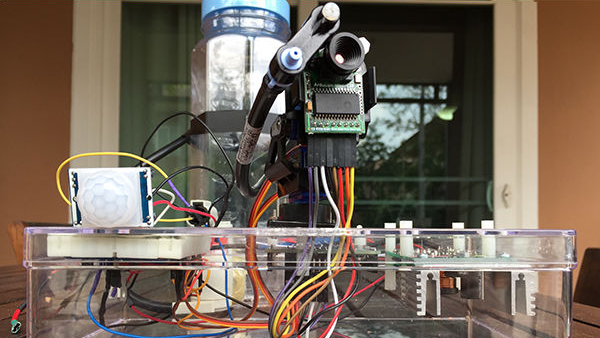
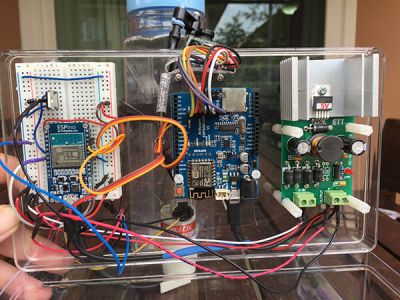
The main component of the security system is a Raspberry Pi fitted with a camera and a Movidius Neural Compute Stick. This allows the Raspberry Pi to run real-time object identification on video. The Raspberry Pi is programmed to raise the alarm if it detects humans approaching, but ignores the family dog and other false targets. In the event of a detection, the Raspberry Pi sends a signal over LoRa to a base station, which sounds an alarm. The pitch of the alarm increases the closer the target gets to the camera, thanks to some simple code with bounding boxes.
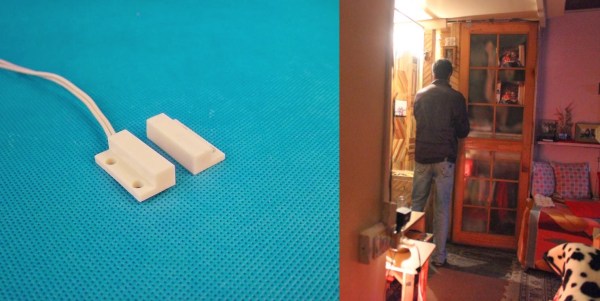
It’s a nifty way to create an intelligent security system, and all the more impressive for being entirely constructed from off-the-shelf parts and code. Neural networks have become increasingly useful; they can even tell when your cat wants to go outside. Video after the break.
Continue reading “Neural Network Smartens Up A Security System”