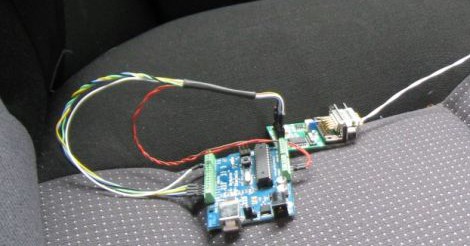
[Matlo] wrote in to share his USB sniffing project using the BeagleBoard-xM. It builds on the Google Summer of Code project from 2010 that used the non-xM version of the hardware to build a pass through USB sniffer. [Matlo] couldn’t get it to work back then, but recently revisited the project. He’s cleaned up some scripts and generally made it a bit easier for others to pull off as well.
The ARM-based BeagleBoard seen above acts as man-in-the-middle. You connect your target USB device to the board and the board to a computer. The board emulates the target device, passing packets in either direction while also logging them. The captured data is in the correct format for display using WireShark, the de facto standard for making sense of captured communication packets.
This is great for figuring out how to use USB devices on non-standard systems, or vice versa.