There’s a laundry list of ways that humans are polluting the earth, and even though it might not look like it from the surface, the oceans seem to bear the brunt of our waste. Some research suggests that plastic doesn’t fully degrade as it ages, but instead breaks down into smaller and smaller bits that will be somewhere the in environment for such a long time it could be characterized in layman’s terms as forever.
Not only does waste of all kinds make its way to the oceans by rivers or simply by outright dumping, but commercial fishing gear is estimated to comprise around 10% of the waste in the great blue seas, and one of the four nonprofits help guide this year’s Hackaday Prize is looking to eliminate some of that waste and ensure it doesn’t cause other problems for marine life. This was the challenge for the Conservation X Labs dream team, three people who were each awarded a $6,000 micro-grant to work full time for two months on the problem.
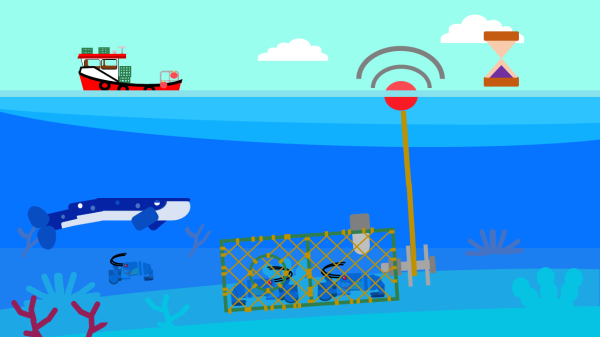
It isn’t about simply collecting waste in the ocean, but rather about limiting the time that potentially harmful but necessary fishing equipment is in the water in the first place. For this two-month challenge, this team focused on long lines used by professional fishing operations to attach buoys to gear like lobster pots or crab traps. These ropes are a danger to large ocean animals such as whales when they get tangled in them and, if the lines detach from the traps, the traps themselves continue to trap and kill marine life for as long as they are lost underwater. This “ghost gear” is harmful in many different ways, and reducing its time in the water or “soak time” was the goal for the project.
Let’s take a closer look at their work after the break, and we can also see the video report they filed as the project wrapped up.