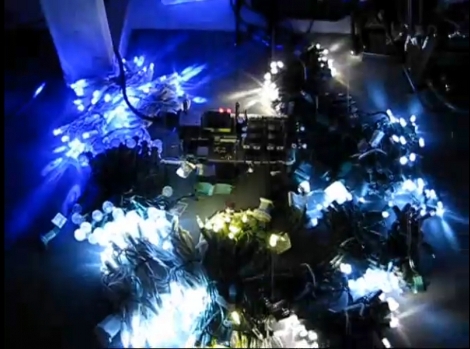
We get a lot of tips about Christmas light controllers but rarely do they contain the kind of juicy detail that [Vince Cappellano] included with his setup. His video explaining the controller he built is embedded after the break and it’s not to be missed.
We think there’s a lot of good design invovled in this porject. First off, he’s got eight physical channels, each with optisolation and a triac for 256 levels of power control. But he was able to double the control to sixteen virtual channels if you’re using LED lighting. That’s because on those strings half of the LEDs are reverse biased compared to the rest. By adding sensing circuitry to the incoming AC, he can switch the triacs to only send positive or negative voltage through the LED strands, which produces the additional virtual channels. And did we mention that he did all this using wire wrapping and point-to-point soldering?