It is the bane of worldwide travel: there isn’t just one way to get AC power from the wall. The exact connector — and what you can expect when you plug in — differs from country to country. Even if you stay home, you must account for this if your designs go places and expect to plug into the wall. If you’ve ever looked at a universal adapter, it is full of prongs and pins like a metallic porcupine. Where do all those pins go?
Of course, there are some easy ways to sidestep the whole issue if you don’t need AC power. Much low-power gear now just provides a USB or barrel connector. Then you can use an area-appropriate adapter or charger to power your device. Batteries work, too. But if you need to plug in, you will run into other kinds of plugs.
Switching power supplies have helped. In the old days, many things expected either 125V or 250V and didn’t work with the opposite voltage. Switching power supplies often allow a wide input range or have a switch to select one range or the other. These two voltages will cover almost any situation. If you have something that must have one voltage or the other, you’ll need a transformer — also called a converter — to step the voltage up or down. But most often, these days, you just need an adapter. There are slight variations. For example, some countries supply 100V or 110V, but that usually doesn’t make much difference. You also need to understand if your equipment cares if the AC is 50 Hz or 60 Hz.
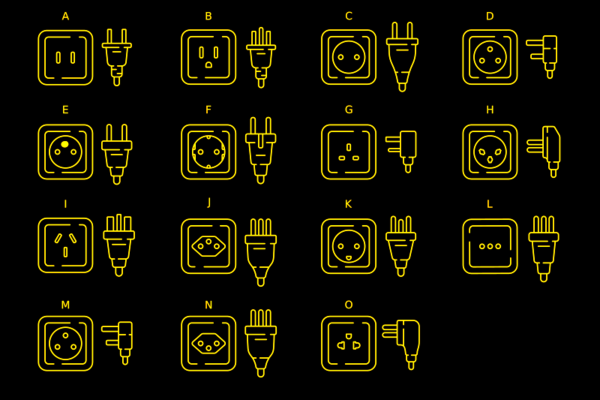
Most of the power sockets you’ll find around the world will fall into one of several categories. The categories range from A to N. Even among these, however, there are variations.
Type A
For example, the common type A plug and socket are what Americans call “two prong.” If you live in the US, you’ve probably noticed that the plug is polarized. That is, one pin is slightly wider than the other so the plug can only go in one way. The wide pin is connected to the circuit neutral. The maximum load for this connector is 15A. It is difficult to find type A sockets anymore, other than on cheap extension cords or things like lamps that pass through their electrical connections to a second socket. Type B is far more common and type A plug will fit in a type B socket.
Continue reading “Tech In Plain Sight: Field Guide To Power Plugs”