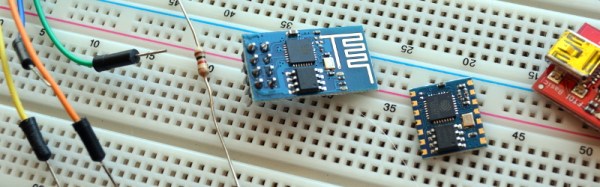
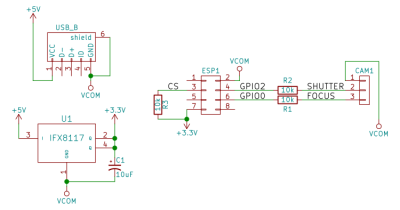
It’s just ridiculous how cheap and easy it is to do some things today that were both costly and difficult just two or three years ago. Case in point: Hackaday.io user [gamaral] built a WiFi remote control for his Canon E3 camera out of just three parts: an ESP8266 module, a voltage regulator, and a stereo plug that the camera uses as its remote trigger.
And the codebase is just about as minimal, although it’s not without its nice touches. Control is easy — just pull down a pin for focus or shutter. The ESP listens to a custom port, and when it gets the message, “presses” or “releases” the pins. It’s a good, simple example of how to work with the ESP IOT SDK.
The timing is all on the client side. [gamaral] knew that he was going to want to play around with how long to hold down the focus button, for instance, so he left that flexible. Using Netcat makes the client-side code completely trivial: echo -n "SHUTTER HOLD" | nc -w 1 -q 1 roosevelt 9021. Bam. And it worked first time. Check the well-done video just below for more details.
And keep your eye on [gamaral]’s Hackaday.io page, because he’s going to make another video when the PCBs arrive in the mail.
Continue reading “Five Bucks, Three Parts: WiFi Camera Remote”

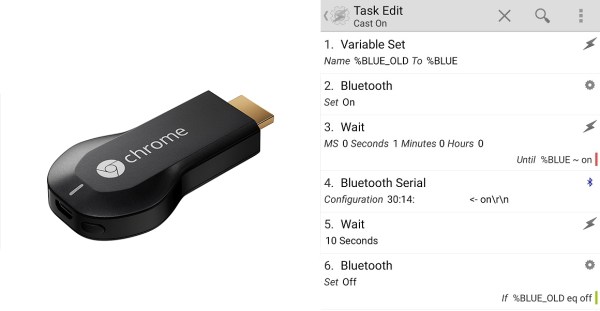
 Now in all honesty, the Chromecast gets hot but the amount of power it draws when not in use is still pretty negligible compared to the draw of your TV. Every watt counts, and [Ilias] took this as an opportunity to refine his skills and combine a system using an Arduino, Bluetooth, and Android to create a robust power switch solution for the Chromecast.
Now in all honesty, the Chromecast gets hot but the amount of power it draws when not in use is still pretty negligible compared to the draw of your TV. Every watt counts, and [Ilias] took this as an opportunity to refine his skills and combine a system using an Arduino, Bluetooth, and Android to create a robust power switch solution for the Chromecast.