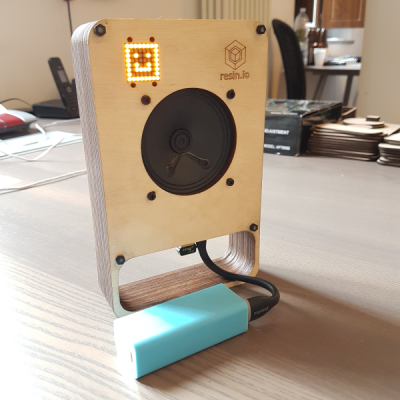
[curcuz]’s BoomBeastic mini is a Raspberry Pi based smart connected speaker. But don’t dis it as just another media center kind of project. His blog post is more of a How-To guide on setting up container software, enabling OTA updates and such, and can be a good learning project for some. Besides, the design is quite elegant and nice.
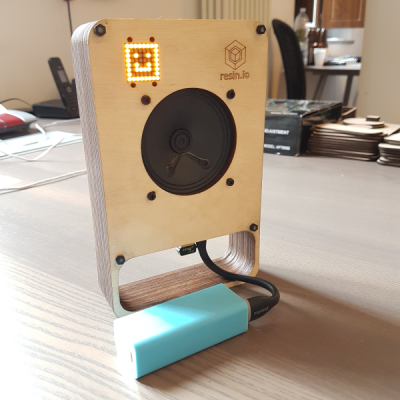 The hardware is simple. There’s the Raspberry-Pi — he’s got instructions on making it work with the Pi2, Pi2+, Pi3 or the Pi0. Since the Pi’s have limited audio capabilities, he’s using a DAC, the Adafruit I2S 3W Class D Amplifier Breakout for the MAX98357A, to drive the Speaker. The I2S used by that part is Inter-IC Sound — a 3 wire peer to peer audio bus — and not to be confused with I2C. For some basic visual feedback, he’s added an 8×8 LED matrix with I2C interface. A Speaker rounds out the BoM. The enclosure is inspired by the Pimoroni PiBow which is a stack of laser cut MDF sheets. The case design went through four iterations, but the final result looks very polished.
The hardware is simple. There’s the Raspberry-Pi — he’s got instructions on making it work with the Pi2, Pi2+, Pi3 or the Pi0. Since the Pi’s have limited audio capabilities, he’s using a DAC, the Adafruit I2S 3W Class D Amplifier Breakout for the MAX98357A, to drive the Speaker. The I2S used by that part is Inter-IC Sound — a 3 wire peer to peer audio bus — and not to be confused with I2C. For some basic visual feedback, he’s added an 8×8 LED matrix with I2C interface. A Speaker rounds out the BoM. The enclosure is inspired by the Pimoroni PiBow which is a stack of laser cut MDF sheets. The case design went through four iterations, but the final result looks very polished.
On the software side, the project uses Mopidy — a Python application that runs in a terminal or in the background on devices that have network connectivity and audio output. Out of the box, it is an MPD and HTTP server. Additional front-ends for controlling Mopidy can be installed from extensions, enabling Spotify, Soundcloud and Google Music support, for example. To allow over-the-air programming, [curcuz] is using resin.io which helps streamline management of devices that are hard to reach physically. The whole thing is containerized using Docker. Additional instructions on setting up all of the software and libraries are posted on his blog post, and the code is hosted on GitHub.
There’s a couple of “To-Do’s” on his list which would make this even more interesting. Synced audio being one: in a multi-device environment, have the possibility to sync them and reproduce the same audio. The other would be to add an Emoji and Equalizer display mode for the LED matrix. Let [curcuz] know if you have any suggestions.
Continue reading “An Eye-Catching Raspberry Pi Smart Speaker” →




 The hardware is simple. There’s the Raspberry-Pi — he’s got instructions on making it work with the Pi2, Pi2+, Pi3 or the Pi0. Since the Pi’s have limited audio capabilities, he’s using a DAC, the
The hardware is simple. There’s the Raspberry-Pi — he’s got instructions on making it work with the Pi2, Pi2+, Pi3 or the Pi0. Since the Pi’s have limited audio capabilities, he’s using a DAC, the