These days, if you’re walking around with a cellphone, you’ve basically fitted an always-on tracking device to your person. That’s even more the case if there happens to be an eavesdropping device in your vicinity. To combat this, the Electronic Frontier Foundation has created Rayhunter as a warning device.
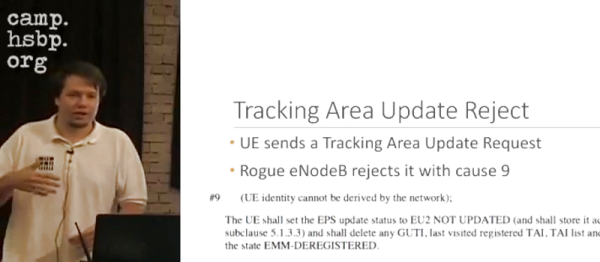
Rayhunter is built to detect IMSI catchers, also known as Stingrays in the popular lexicon. These are devices that attempt to capture your phone’s IMSI (international mobile subscriber identity) number by pretending to be real cell towers. Information on these devices is tightly controlled by manufacturers, which largely market them for use by law enforcement and intelligence agencies.

To run Rayhunter, all you need is an Orbic RC400L mobile hotspot, which you can currently source for less than $30 USD online. Though experience tells us that could change as the project becomes more popular with hackers. The project offers an install script that will compile the latest version of the software and flash it to the device from a computer running Linux or macOS — Windows users currently have to jump through a few extra hoops to get the same results.
Rayhunter works by analyzing the control traffic between the cell tower and the hotspot to look out for hints of IMSI-catcher activity. Common telltale signs are requests to switch a connection to less-secure 2G standards, or spurious queries for your device’s IMSI. If Rayhunter notes suspicious activity, it turns a line on the Orbic’s display red as a warning. The device’s web interface can then be accessed for more information.
While IMSI catchers really took off on less-secure 2G networks, there are developments that allow similar devices to work on newer cellular standards, too. Meanwhile, if you’ve got your own projects built around cellular security, don’t hesitate to notify the tipsline!