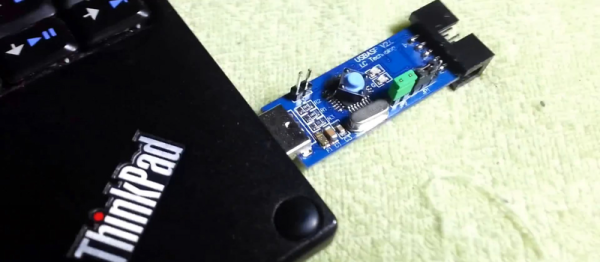
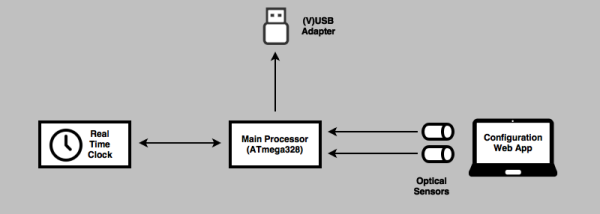
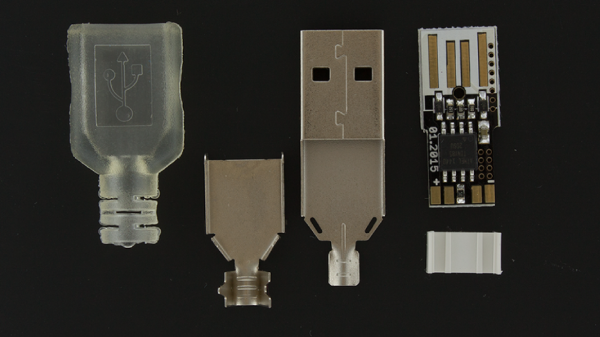
It might not seem too impressive these days, but when microcontrollers with hardware USB support were more expensive and rare, the VUSB library was often used to create USB devices with an ATtiny85. It became so popular that the ATtiny85 even got packaged into USB dongle formfactors, like the DigiSpark boards. Well, you might not know this, but your Android smartphones can also work with USB mice and touchscreens in lieu of the built-in touchscreen display. [ErfanSn] combined these two ideas, creating a library to automate smartphone touchscreen events and keyboard input with an ATtiny85 — open for all of us to use, and with examples to spare.
The library is called DigiCombo, and it comes with plenty of examples for any screen touch event emulation that you might want. For instance, check out the README — it has video examples for Instagram page scrolling, unlock screen brute-forcing with random coordinates, playing the Stack rhythm game, and pinch zoom — all the building blocks for your smartphone touch emulation needs are covered pretty well! Of course, all of these have example code corresponding to them, that you can download and base your own ideas on. What’s more, the library is available in current Arduino IDE under the DigiCombo name. So if you need to, say, make a quick autoclicker for your phone, the library is a few steps away!
If your smartphone project was stalled because you needed to emulate touchscreen input, this library is your chance to get it done! We appreciate projects that let us get more from smartphones — there’s a lot of those laying around, they’re pretty functional and self-sufficient devices, so it makes sense that some projects of ours could do with a phone instead of a Raspberry Pi. Some manufacturers let us get a bit more of our phones, but this hasn’t really caught on, which means we have to make do with help of libraries like these. Or, perhaps, you rely on your phone day-to-day, and you’d like to add a touchpad to its back?