A team of researchers at the University of Texas at Dallas have come up with an ingenious way to make a low-cost, high strength, artificial muscle. Their secret? Fishing line. The study was just published today in the journal Science, and the best part is they describe how to recreate it at home.
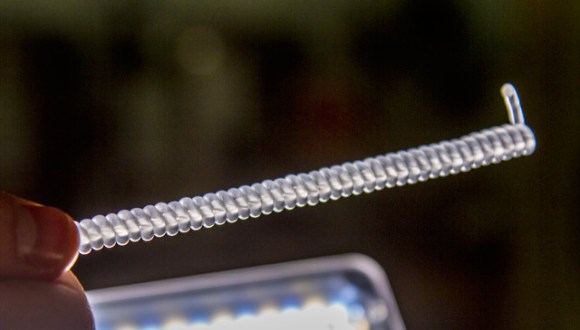
To create it, the researchers take regular fishing line (polyethylene or nylon string) and twist it under tension until it curls up into a tightly formed spring. It can then be temperature treated to lock in this position.
When heated again, the plastic tries to untwist — the peculiar thing is, this causes the entire coil to compress — think of it as Chinese finger-trap. Polyethylene and nylon molecules also contract lengthwise when heated. It can contract up to about 49%, with as much pulling power as 100 times its equivalent human muscle in weight. This equates to about 5.3 kilowatts of mechanical work per kilogram of muscle weight — similar to the output of a jet engine.
Stick around to see the video of how to make it — we’re excited to see what you guys think up for project applications!
Continue reading “Researchers Create Synthetic Muscle 100 Times Stronger Than The Real Thing”



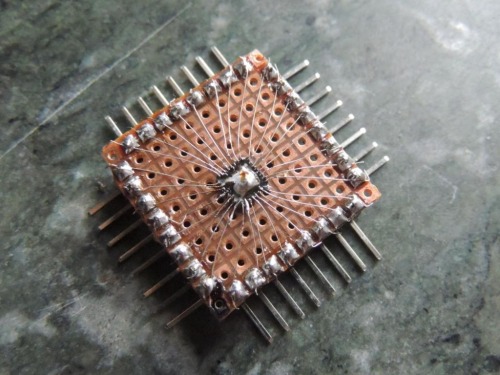 What do you do when you have ATMega328s in QFN package burning a hole in your bug box, but you aren’t set up for SMD and have limited access to parts? You man up and do what [Djpanjan] did:
What do you do when you have ATMega328s in QFN package burning a hole in your bug box, but you aren’t set up for SMD and have limited access to parts? You man up and do what [Djpanjan] did: 









