Flexible circuits have been around longer than you might expect, although they only recently rounded the bend and bounced into the hobbyist’s toolbox. When Boldport fanatic [Laura Lindzey] found out about them, her immediate dream project was to make an origami butterfly that does something cool, though she wasn’t sure what.
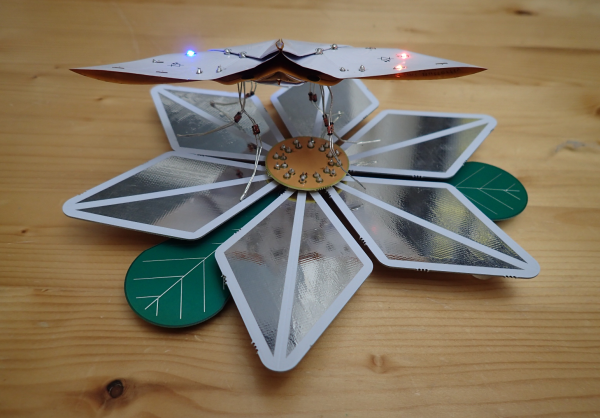
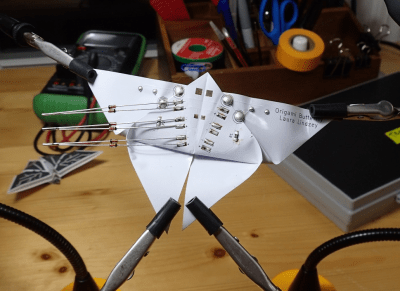 The idea she landed on is this: when the butterfly alights on a power-providing flower, it draws electrical nectar through its diode legs and lights up the LEDs on its wings. As long as one leg touches a ground petal and another touches a VIN petal, there will be light.
The idea she landed on is this: when the butterfly alights on a power-providing flower, it draws electrical nectar through its diode legs and lights up the LEDs on its wings. As long as one leg touches a ground petal and another touches a VIN petal, there will be light.
Though the idea may be simple, it’s the execution that’s mind-bending. After meticulous planning and a lot of paper prototyping, she sent off the gerbers and got version one back. The circuit worked, but assembly was tedious — not what you want when you’re trying to stay friendly with the other people in your PCB exchange club.
We imagine that hard creases are probably not what the flexible PCB purveyors have in mind, but this origami butterfly is an awesome exercise in what can be done with flexible PCBs. Not only that, it’s a great insight into some design rules where almost none exist, learned through firsthand experience. Every technology can benefit from trailblazers like [Laura].
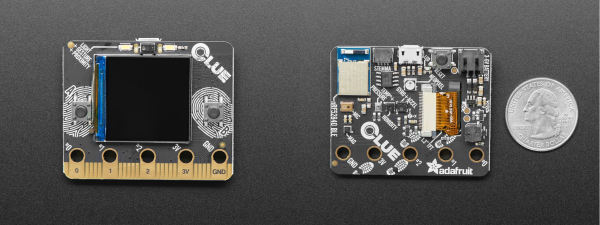
If you want to do some flexible prototyping at home, just print your own pliable PCBs.