More and more clubs are going digital. When you go out to hear a band, they’re plugging into an ADC (analog-to-digital converter) box on stage, and the digitized audio data is transmitted to the mixing console over Ethernet. This saves the venue having to run many audio cables over long distances, but it’s a lot harder to hack on. So [Michael] trained popular network analysis tools on his ProCo Momentum gear to see just what the data looks like.
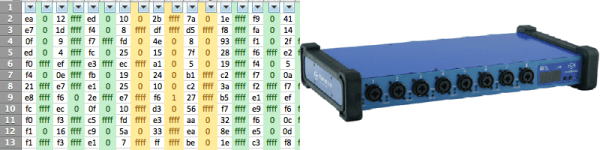
[Michael]’s writeup of the process is a little sparse, but he name-drops all the components you’d need to get the job done. First, he simply looks at the raw data using Wireshark. Once he figured out how the eight channels were split up, he used the command-line version (tshark) and a standard Unix command-line tool (cut) to pull the data apart. Now he’s got a text representation for eight channels of audio data.
Using xxd to convert the data from text to binary, he then played it using sox to see what it sounded like. No dice, yet. After a bit more trial and error, he realized that the data was unsigned, big-endian integers. He tried again, and everything sounded good. Success!
While this is not a complete reverse-engineering tutorial like this one, we think that it hits the high points: using a bunch of the right tools and some good hunches to figure out an obscure protocol.

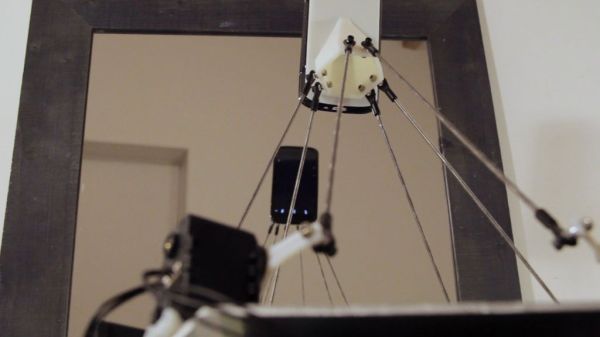
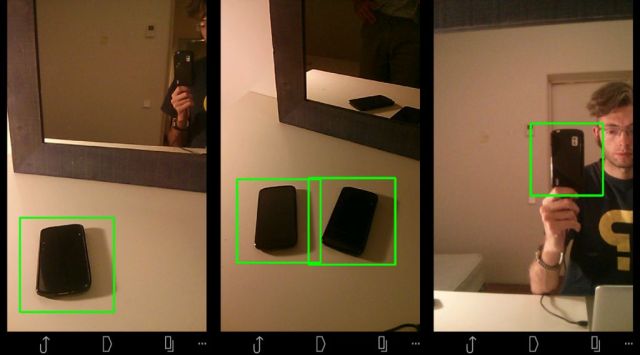 Hardware-wise, the #selfie bot is a Stewart platform made from six servo motors and a few pieces of carefully measured pushrod connected with swivel-ball-links. An android phone is mounted on the end effector which acts functionally as the robot’s face and eyes. To make it self-aware in a sense, [Ajna] and [Hersan] created their own recognition software with Open CV using a collection of sample images of various phones as reference points. As soon as the robot recognizes itself in the mirror as indicated by specific words flashing on its screen, it takes a picture, immediately uploading it to its own
Hardware-wise, the #selfie bot is a Stewart platform made from six servo motors and a few pieces of carefully measured pushrod connected with swivel-ball-links. An android phone is mounted on the end effector which acts functionally as the robot’s face and eyes. To make it self-aware in a sense, [Ajna] and [Hersan] created their own recognition software with Open CV using a collection of sample images of various phones as reference points. As soon as the robot recognizes itself in the mirror as indicated by specific words flashing on its screen, it takes a picture, immediately uploading it to its own