The recent Supercon 6 badge, if you haven’t seen it, was an old-fashioned type computer with a blinky light front panel. It was reminiscent of an Altair 8800, a PDP-11, or DG Nova. However, even back in the day, only a few people really programmed a computer with switches. Typically, you might use the switches to toggle in a first-level bootloader that would then load a better bootloader from some kind of storage like magnetic or paper tape. Most people didn’t really use the switches.
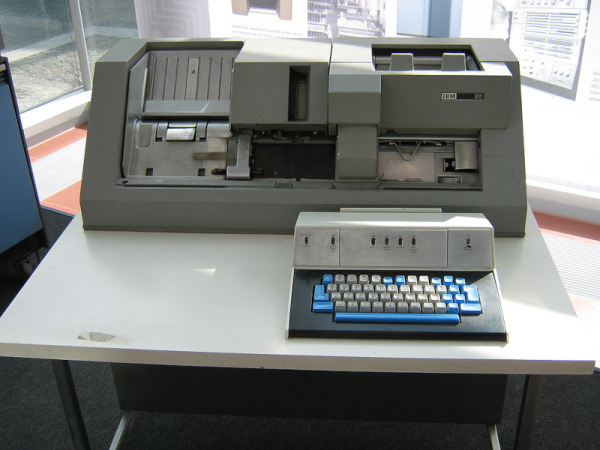
What most people did do, however, was punch cards. Technically, Hollerith cards, although we mostly just called them cards, punched cards, or IBM cards. There were a lot of different machines you could use to punch cards, but none were as popular, I would guess, as the IBM 029. Certainly, the models in the series were overwhelmingly what people used to punch cards.
For the uninitiated, a card was about the size of an old-fashioned dollar bill — the ones in style when Herman Hollerith invented them. The card was made of material not quite as thick as a standard file folder and was divided into 80 columns and 12 rows. Later cards had more columns, but those never really caught on to the same scale as the classic 80-column card. Continue reading “Retrotechtacular: Programming By Card”