Well, this week’s Links article is likely to prove a bit on the spicy side, thanks in no small part to the Chinese balloon that spent the better part of the week meandering across the United States. Putting aside the politics of the whole thing — which we’ll admit is hard to do, given the state of the world today — there are some interesting technical aspects to this story, which the popular press has predictably ignored. Like the size of this thing — it’s enormous. This is not even remotely on the same scale as the hundreds of radiosonde-carrying balloons sent aloft every day, at least if the back-of-the-envelope math thoughtfully sent to us by [Dr_T] holds up. If the “the size of three buses” description given in most media reports is accurate, that means a diameter of about 40 meters, for a volume of 33,500 cubic meters. If it’s filled with helium — a pretty safe bet — that makes its lifting capacity something like three metric tons. So maybe it was a good idea to wait until it was off the Carolinas to shoot it down.
Hackaday Columns4727 Articles
This excellent content from the Hackaday writing crew highlights recurring topics and popular series like Linux-Fu, 3D-Printering, Hackaday Links, This Week in Security, Inputs of Interest, Profiles in Science, Retrotechtacular, Ask Hackaday, Teardowns, Reviews, and many more.
Copyright Data, But Do It Right
Copyright law is a triple-edged sword. Historically, it has been used to make sure that authors and rock musicians get their due, but it’s also been extended to the breaking point by firms like Disney. Strangely, a concept that protected creative arts got pressed into duty in the 1980s to protect the writing down of computer instructions, ironically a comparatively few bytes of BIOS code. But as long as we’re going down this strange road where assembly language is creative art, copyright law could also be used to protect the openness of software as well. And doing so has given tremendous legal backbone to the open and free software movements.
So let’s muddy the waters further. Looking at cases like the CDDB fiasco, or the most recent sale of ADSB Exchange, what I see is a community of people providing data to an open resource, in the belief that they are building something for the greater good. And then someone comes along, closes up the database, and sells it. What prevents this from happening in the open-software world? Copyright law. What is the equivalent of copyright for datasets? Strangely enough, that same copyright law.
Data, being facts, can’t be copyrighted. But datasets are purposeful collections of data. And just like computer programs, datasets can be licensed with a restrictive copyright or a permissive copyleft. Indeed, they must, because the same presumption of restrictive copyright is the default.
I scoured all over the ADSB Exchange website to find any notice of the copyright / copyleft status of their dataset taken as a whole, and couldn’t find any. My read is that this means that the dataset is the exclusive property of its owner. The folks who were contributing to ADSB Exchange were, as far as I can tell, contributing to a dataset that they couldn’t modify or redistribute. To be a free and open dataset, to be shared freely, copied, and remixed, it would need a copyleft license like Creative Commons or the Open Data Commons license.
So I’ll admit that I’m surprised to have not seen permissive licenses used around community-based open data projects, especially projects like ADSB Exchange, where all of the software that drives it is open source. Is this just because we don’t know enough about them? Maybe it’s time for that to change, because copyright on datasets is the law of the land, no matter how absurd it may sound on the face, and the closed version is the default. If you want your data contributions to be free, make sure that the project has a free data license.
Hackaday Podcast 204: Cesium, Colorful Cast Buttons, And CNC Pizza
This week, Editor-in-Chief Elliot Williams and Assignments Editor Kristina Panos met up over thousands of miles to discuss the hottest hacks of the past seven days. There’s a whole lot of news this week, and the really good part is the the small radioactive source that went missing in Australia has been found. Phew!
Kristina is still striking out on What’s That Sound, but we’re sure you’ll fare better. If you think you know what it is, fill out the form and you’ll be entered to win a coveted Hackaday Podcast t-shirt!
Finally, we get on to the hacks with an atomic pendulum clock that’s accurate enough for CERN, safecracking the rough-and-ready way, and plenty of hacks that are non-destructive to nice, old things. We’ll gush over a tiny DIY adjustable wrench, drool over CNC pizza, and rock out to the sounds of a LEGO guitar/synthesizer thing.
Check out the links below if you want to follow along, and as always, tell us what you think about this episode in the comments!
And/or download it and listen offline.
Continue reading “Hackaday Podcast 204: Cesium, Colorful Cast Buttons, And CNC Pizza”
This Week In Security: Github, Google, And Realtek
GitHub Desktop may have stopped working for you yesterday, Febuary 2nd. The reason was an unauthorized access to some decidedly non-public repositories. The most serious bit of information that escaped was code signing certificates, notably used for GitHub Desktop and Atom. Those certificates were password protected, so it’s unlikely they’ve been abused yet. Even so, Github is taking the proper steps of revoking those certificates.
The only active certificate that was revoked was used for signing the Mac releases of GitHub Desktop, so quite a few older versions of that software is no longer easily installed. If nothing else, it’s a reminder that even a project with a well run security team can have problems.
Sh1mmer-ing Chromebooks
There’s a new, clever attack on the Chromebook, specifically with the goal of unenrolling the device from an educational organization. And the “vulnerability” is a documented feature, the RMA Shim. That’s a special boot loader target that contains a valid signature, but allows the booting of other code, intended for troubleshooting and fixing devices in a repair center. Quite a few of those images have leaked, and Sh1mmer combines the appropriate image with a boot menu with some interesting options.
The first is unenrolling, so the device will act like a privately owned computer. This gets rid of content blocks and allows removing extensions. But wait, there’s more. Like rooting the device, a raw Bash terminal, and re-enabling developer mode. Now, as far as we can tell, this doesn’t *directly* break device encryption, but it’s likely that the RMA shim could be abused to tamper with the device’s filesystem. Meaning that the leak of a bunch of signed shims is a big problem for device security. If you use a Chromebook, it might be time to do some research on whether that model’s shim has been leaked. Continue reading “This Week In Security: Github, Google, And Realtek”
China’s New 100 MPH Train Runs On Hydrogen And Supercaps
Electric cars are very much en vogue right now, as the world tries to clean up on emissions and transition to a more sustainable future. However, these vehicles require huge batteries as it is. For heavier-duty applications like trucks and trains, batteries simply won’t cut the mustard.
Normally, the solution for electrifying railways is to simply string up some wires and call it a day. China is trying an alternative solution, though, in the form of a hydrogen-powered train full of supercapacitors.
Continue reading “China’s New 100 MPH Train Runs On Hydrogen And Supercaps”
Driverless Buses Take To The Road In Scotland
Scotland! It’s the land of tartans, haggis, and surprisingly-warm kilts. It’s also ground zero for the first trial of full-sized driverless buses in the United Kingdom.
It’s not just automakers developing driverless technologies. Transit companies are desperate to get in on the action because it would completely upend their entire existing business structure. Now that self-driving buses are finally approaching a basic level of competence, they’re starting to head out to haul passengers from A to B. Let’s look at how the UK’s first driverless bus project is getting on out in the real world.
Continue reading “Driverless Buses Take To The Road In Scotland”
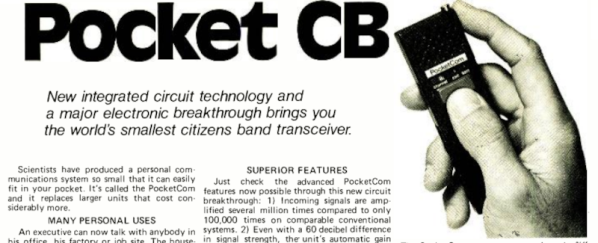
Retro Gadgets: The CB Cell Phone
There was a time when one of the perks of having a ham radio in your car (or on your belt) was you could make phone calls using a “phone patch.” In the 1970s, calling someone from inside your parked car turned heads. Now, of course, it is an everyday occurrence thanks to cell phones. But in 1977, cell phones were nowhere to be found. Joseph Sugarman, the well-known founder of JS&A, saw a need and wanted to fill it. So he offered the “PocketCom CB” which was billed as the “world’s smallest citizens band transceiver.” You can see the full-page ad from 1977 below.
Remember that this is from an era when ICs that could operate at 30 MHz were not the norm, so you have to temper your expectations. The little unit was 5.5 in by 1.5 in and less than an inch thick. That’s actually not bad, but you had — optimistically — 100 mW of output power. They claimed the N cell batteries would last two weeks with average use, but we imagine a lot less as soon as you start transmitting. The weight was 5 oz, but we suspect that is without the batteries.