There’s a paradox in amateur radio: after all the time and effort spent getting a license and all the expense of getting some gear together, some new hams suddenly find that they don’t have a lot to talk about when they get in front of the mic. While that can be awkward, it’s not a deal-breaker by any means, especially when this Pi Pico SSTV decoder makes it cheap and easy to get into slow-scan television.
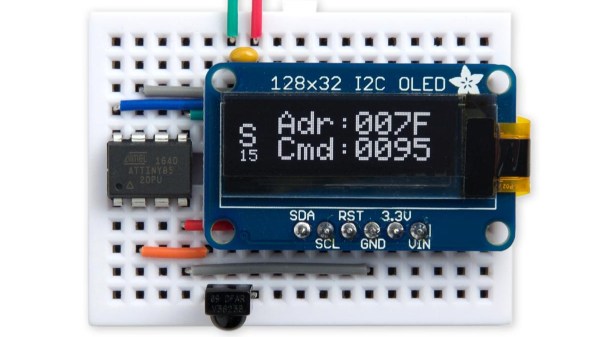
There’s not much to [Jon Dawson]’s SSTV decoder. Audio from a single-sideband receiver goes through a biasing network and into the Pico’s A/D input. The decoder can handle both Martin and Scottie SSTV protocols, with results displayed on a TFT LCD screen. The magic is in the software, of course, and [Jon] provides a good explanation of the algorithms he used, as well as some of the challenges he faced, such as reliably detecting which protocol is being used. He also implemented correction for “slant,” which occurs when the transmitter sample rate drifts relative to the receiver. Fixing that requires measuring the time it took to transmit each line and adjusting the timing of the decoder to match. The results are dramatic, and it clears up one of the main sources of SSTV artifacts.
We think this is a great build, and simple enough that anyone can try it. The best part is that since it’s receive-only, it doesn’t require a license, although [Jon] says he’s working on an encoder and transmitter too. We’re looking forward to that, but in the meantime, you might just be able to use this to capture some space memes.