[Editor’s note: There’s an ongoing back-and-forth about this “spyware” right now. We haven’t personally looked into it on any phones, and decoded Wireshark caps of what the cleaner software sends home seem to be lacking — it could be innocuous. We’re leaving our original text as-run below, but you might want to take this with a grain of salt until further evidence comes out. Or keep us all up to date in the comments. But be wary of jumping to quick conclusions.]
Samsung may have the highest-end options for hardware if you want an Android smartphone, but that hasn’t stopped them from making some questionable decisions on the software they sometimes load on it. Often these phones come with “default” apps that can’t be removed through ordinary means, or can’t even be disabled, and the latest discovery related to pre-loaded software on Samsung phones seems to be of a pretty major security vulnerability.
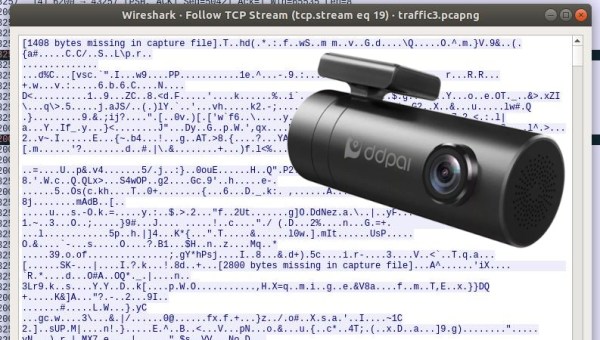
This software in question is a “storage cleaner” in the “Device Care” section of the phone, which is supposed to handle file optimization and deletion. This particular application is made by a Chinese company called Qihoo 360 and can’t be removed from the phone without using ADB or having root. The company is known for exceptionally bad practices concerning virus scanning, and the software has been accused of sending all information about files on the phone to servers in China, which could then turn all of the data it has over to the Chinese government. This was all discovered through the use of packet capture and osint, which are discussed in the post.
These revelations came about recently on Reddit from [kchaxcer] who made the original claims. It seems to be fairly legitimate at this point as well, and another user named [GeorgePB] was able to provide a temporary solution/workaround in the comments on the original post. It’s an interesting problem that probably shouldn’t exist on any phone, let alone a flagship phone competing with various iPhones, but it does highlight some security concerns we should all have with our daily use devices when we can’t control the software on the hardware that we supposedly own. There are some alternatives though if you are interested in open-source phones.
Thanks to [kickaxe] for the tip!
Photo from Pang Kakit [CC BY-SA 3.0 DE (https://creativecommons.org/licenses/by-sa/3.0/de/deed.en)]