Are you ready for a tale of poorly supported hardware, clueless contractors, and bad coding? Look no further than [Neighborino]’s excellent write-up where he details his pursuit of smart home pwnership.
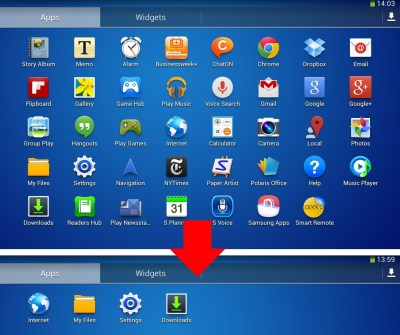
[Neighborino]’s smart home system controls the windows, blinds, outlets, and HVAC. But by the time the high-rise apartment was ready for occupancy in 2015, the smart home controllers were already showing their age. You see, the contractor had installed an app to run the home’s programmable logic controllers (PLCs) on stock Galaxy Tab 3 hardware. Yes, that’s a tablet originally released in 2013. They then built the tablets into the wall of each apartment, dooming the homeowner to rely on the vendor forevermore.
It was not long before [Neighborino] and their fellow residents were dealing with stability problems. Bloatware from both Samsung and Google was causing major slowdowns, and the PLC system’s unpublished WiFi password prevented replacement of the controllers.
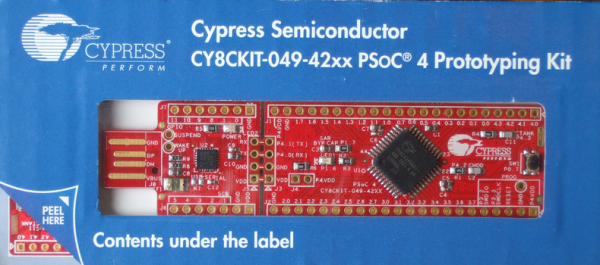
Being an Android developer by trade, [Neighborino] set siege to the walled garden before him. The writeup details the quest to execute what would be a straightforward hack on anything but the x86 hardware that was being targeted.
The first fruit of [Neighborino]’s efforts was a hack for the aged tablets that would display the WiFi password, allowing owners to connect their own controllers to their smart homes. Of course, this is Hackaday, so you know that [Neighborino] didn’t stop there.
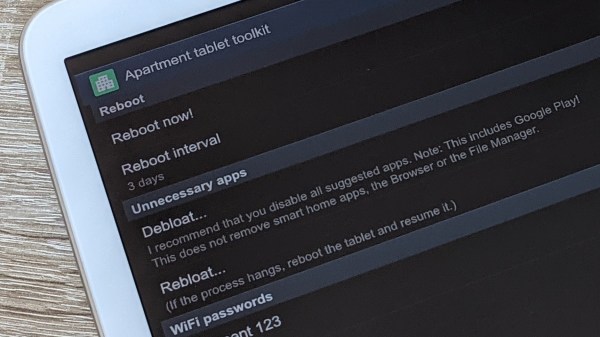
Despite having to deal with two different versions of Android and tablets that were built into the wall of the apartments of non-hacker neighbors, [Neighborino] succeeded in sideloading an APK. This freed them from the shackles of the company that installed the original system and gets longer life out of their Snowden-era Samsungs. A de-bloating tool frees up memory and restores the systems to a nearly performant status. A reboot scheduler keeps the x86 tablets running without user intervention, and of course the WiFi password revealer makes yard waste out of the previously walled garden.
If Smart Home hacks are your thing, we recently covered a Voice Controlled Smart Home setup, and less recently another that combined a Smart Home with a Dumb Terminal. Be sure to share your own smart home hacks with us via the Tip Line!