When building autonomous airborne vehicles like drones or UAVs, saving a little bit of weight goes a long way, literally. Every gram saved means less energy needed to keep the aircraft aloft and ultimately more time in the air, but unmanned vehicles often need to compromise some on weight in order to carry increased computing abilities. Thankfully this one carries a dizzying quantity of computer power for an absolute minimum of weight, and has some clever design considerations to improve its performance as well.
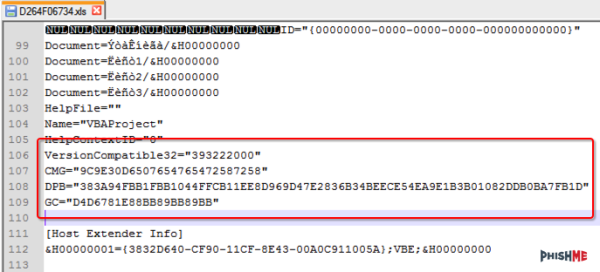
The advantage of this board compared to other similar offerings is that it is built to host a Raspberry Pi Compute Module 4, while the rest of the flight controllers are separated out onto a single circuit board. This means that the Pi is completely sandboxed from the flight control code, freeing up computing power on the Pi and allowing it to run a UAV-specific OS like OpenHD or RubyFPV. These have a number of valuable tools available for unmanned flight, such as setting up a long range telemetry and camera links. The system itself supports dual HD camera input as well as additional support for other USB devices, and also includes an electronic speed controller mezzanine which has support for quadcopters and fixed wing crafts.
Separating non-critical tasks like cameras and telemetry from the more important flight controls has a number of benefits as well, including improved reliability and simpler software and program design. And with a weight of only 30 grams, it won’t take too much cargo space on most UAVs. While the flight computer is fairly capable of controlling various autonomous aircraft, whether it’s a multi-rotor like a quadcopter or a fixed wing device, you might need a little more computing power if you want to build something more complicated.