Readers who took part in the glory days of custom PC building will no doubt remember the stress of having to pick a case for their carefully-curated build. You may have wanted to lower the total cost a bit by getting a cheap case, but then you’d be stuck looking at some econo-box day in and day out. Plus, how do you post pictures online to boast about your latest build if there are no transparent windows and a lighting kit?
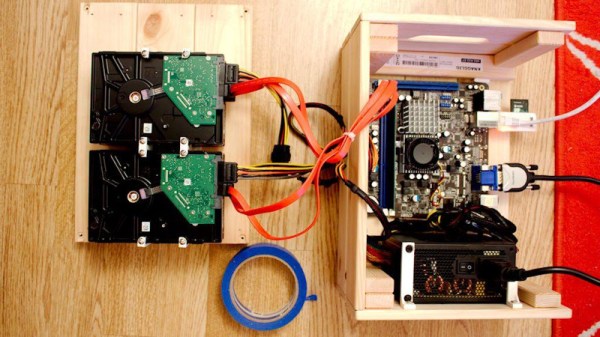
While some may have spent more time choosing their lighted case fans than their optical drive, [Miroslav Prašil] was surely not one of them. When he decided to build a new NAS for his home network, [Miroslav] decided he wanted to put all his money into the device’s internals, and house his build in a wooden storage crate from IKEA. While the low cost was certainly a major factor in the decision, it turns out the crate actually offers a decent amount of room for hardware components. As an added bonus, it doesn’t look completely terrible sitting out in the living room.
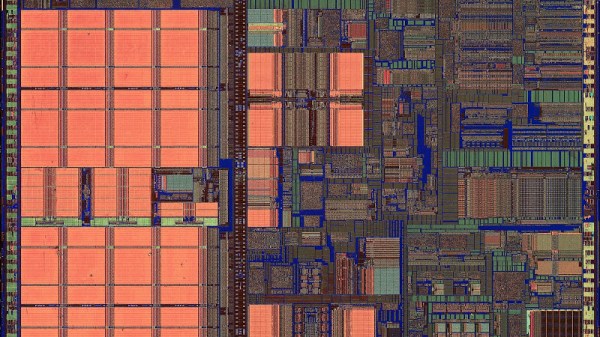
 In a detailed series of posts on his blog, [Miroslav] walks us through the entire process of building what he has come to call the “NAScrate”. Wanting gigabit Ethernet and a real SATA controller, [Miroslav] went for the ASRock C70M1, a Mini-ITX board with integrated dual-core AMD processor. While not exactly a powerhouse, it will certainly wipe the floor with the fruit-inspired single board computers that so often dominate these types of builds.
In a detailed series of posts on his blog, [Miroslav] walks us through the entire process of building what he has come to call the “NAScrate”. Wanting gigabit Ethernet and a real SATA controller, [Miroslav] went for the ASRock C70M1, a Mini-ITX board with integrated dual-core AMD processor. While not exactly a powerhouse, it will certainly wipe the floor with the fruit-inspired single board computers that so often dominate these types of builds.
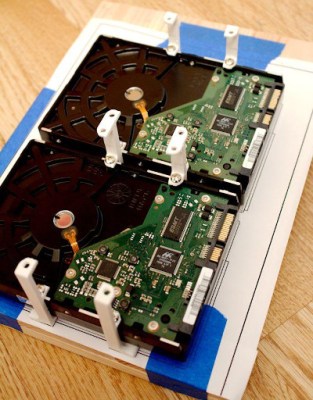
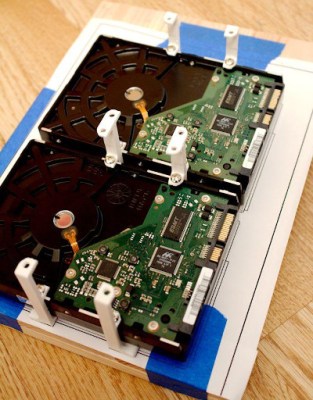
To get his clearances worked out, [Miroslav] rendered the entire build in OnShape, which gave him enough confidence in his design to move on to actual construction. The build involves several 3D printed parts, most notably some clever hard drive mounting brackets which allow the drives to be stacked into a space-saving arrangement while still leaving room for airflow between them.
[Miroslav] deftly avoids any religious debates by leaving off his particular choice for software and operating system on his newly constructed NAS, but he does mention that something like FreeNAS would be a logical choice.
While this may be the first wooden one we’ve covered so far, home servers in general are a favorite project for hackers, from budget-friendly scratch builds all the way up to re-purposed enterprise hardware.