When looking at the piles of cheap RGB, Bluetooth-controlled LED strips you can find for sale just about anywhere these days, integrating them into a home-automation setup is very tempting. Normally these strips are controlled via a special smartphone app, that speaks whatever dodgy protocol was thrown together for the LED strip controller in question. Reverse-engineering this Bluetooth protocol is fairly easy these days, as [Will Cooke] describes in a recent tutorial, although for him there was a bit of a tragic ending with one particular RGB set.
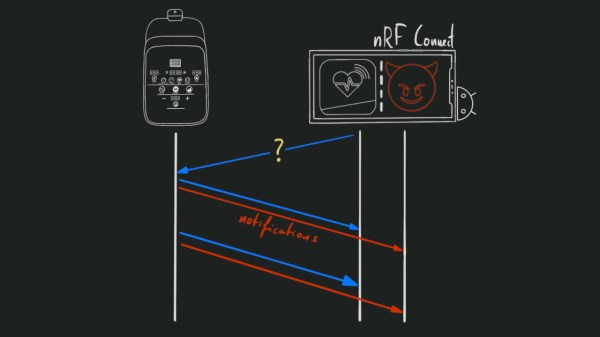
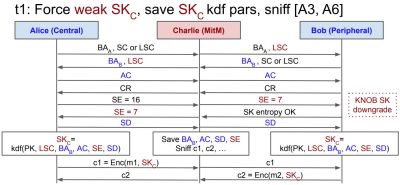
With previous experiences reverse-engineering the Bluetooth protocol with Wireshark under his belt and having published the BJ_LED repository for LED strips that use the MohuanLED app, reverse-engineering this new LED strip with the associated “iDeal LED” app seemed fairly routine. Initially it was indeed routine, with just a curveball in the form of some encryption that the Jadx decompiler used on the app couldn’t help with. Fortunately the key ended up floating around on the internet, and the protocol was wide open. That’s when disaster struck.
While trying to throw payloads at the LED controller to find hidden modes and settings, [Will] found that he could indeed increase the brightness beyond what the app supported, but poking at lighting modes beyond the 10 presets gave a nasty shock. Modes 1 through 10 worked fine, 11 also did something new, but when the controller was asked to switch to mode 12, it shut off. Permanently. Whether this corrupted the firmware or caused some other issue is unknown, but it’s a clear warning that reverse-engineering comes with potentially fried hardware.
We hope that [Will] can get an autopsy performed on this controller to see the cause of this seemingly permanent failure that persisted across hard resets and disconnecting from power overnight. The protocol for this controller has been published on GitHub for those who’d like to take their chances.
LED lights: LadyAda, CC BY-SA 4.0.