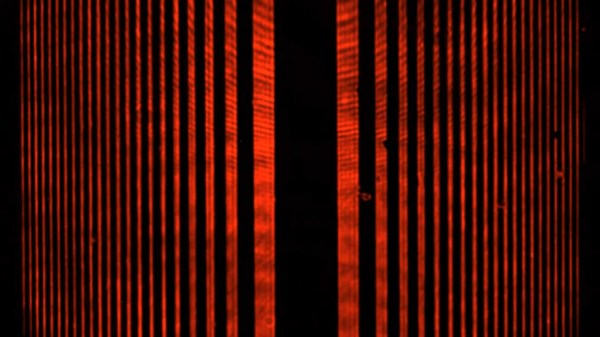
If there’s anything more annoying to an amateur radio operator than noise, we’re not sure what it could be. We’re talking about radio frequency noise, of course, the random broadband emissions that threaten to make it almost impossible to work the bands and pick out weak signals. This man-made interference is known as “QRM” in ham parlance, and it has become almost intolerable of late, as poorly engineered switch-mode power supplies have become more common.
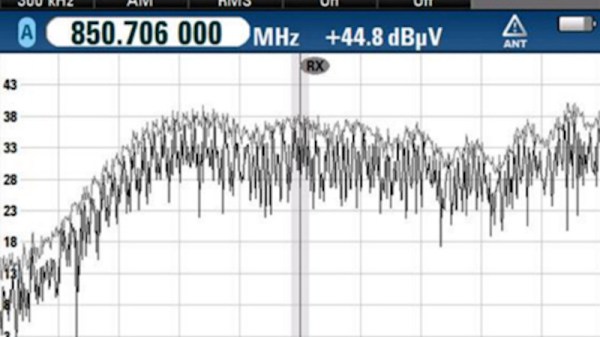
But hams love a technical challenge, so when a nasty case of QRM raised its ugly head, [Kevin Loughlin (KB9RLW)] fought back. With an unacceptable noise floor of S8, he went on a search for the guilty party, and in the simplest way possible — he started flipping circuit breakers. Sure, he could have pulled out something fancier like a TinySA spectrum analyzer, but with his HF rig on and blasting white noise, it was far easier to just work through the circuits one by one to narrow the source down. His noise problem went away with the living room breaker, which led to pulling plugs one by one until he located the culprit: a Roomba vacuum’s charging station.
Yes, this is a simple trick, but one that’s worth remembering as at least a first pass when QRM problems creep up. It probably won’t help if the source is coming from a neighbor’s house, but it’s a least worth a shot before going to more involved steps. As for remediation, [Kevin] opts to just unplug the Roomba when he wants to work the bands, but if you find that something like an Ethernet cable is causing your QRM issue, you might have to try different measures.