Pedals are a great way to control functions on your computer. You’re rarely using your feet for anything else, so they can handle some tasks, freeing up your hands. This Elgato Stream Deck controller from [DDRBoxman] does just that.
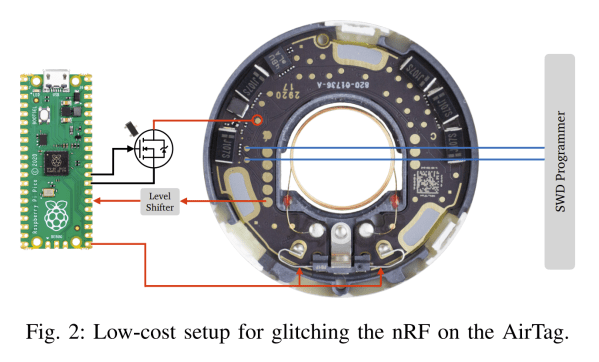
[DDRBoxman] wanted to control Elgato Stream Deck much like the offical pedal sold by the company. Thus, some hacking was in order. Using Wireshark with the Elgato pedal helped to determine the communication method of the real hardware.
Once the protocol was figured out, it was just a task of getting the Raspberry Pi Pico to replicate the same functionality. With the help of the tinyusb library, [DDRBoxman] was able to emulate the real Elgato device successfully. Paired with a 3D-printed footswitch design from Adafruit, and the project was functional and complete.
We’ve seen great foot pedal devices over the years, from a simple macro device to a super-useful page turner for sheet music. If you’ve been hacking away at your own nifty input devices, be sure to drop us a line!