[jamesone111] bought a Transcend WifiSD card, presumably for photography, but it may just have been because he heard that they’re actually tiny Linux servers.
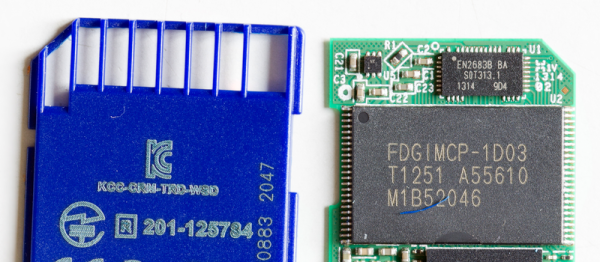
He read a post about these cards on the OpenWRT forums. They’re all a similar configuration of a relatively large amount of memory (compared to the usual embedded computer), a WiFi chip, and an ARM processor running a tiny Linux install. The card acts as a WiFi access point with a little server running on it, and waits for the user to connect to it via a website. It also has a mode where it will connect to up to three access points specified by the user, but it doesn’t actually have a way to tell the user what its IP address is; which is kind of funny.
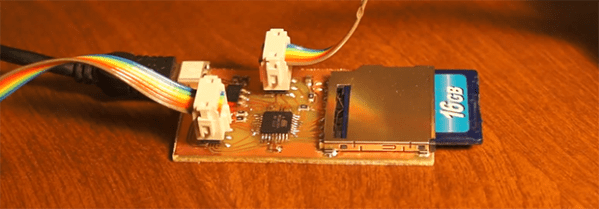
[jamesone111] hacked around with the Transcend card for a bit. He found it pretty insecure, which as long as you’re not a naked celebrity, shouldn’t be a huge issue. For the hacker this is great as it opens up the chance of hacking the firmware for other uses.
Some have already pulled off some cool hacks with these cards. For example, [peterburk] hacked a similar card by PQI to turn his iPod into a portable file server.