You know how you can fall down a rabbit hole when you start on a project? [Fabian Bräunlein] and [Luca Melette] were looking at a box on a broken streetlamp in Berlin. The box looked like a relay, and it contained a radio. It was a Funkrundsteueremfänger – a radio controlled power controller – made by a company called EFR. It turns out that these boxes are on many streetlamps in many cities, and like you do, they thought about how cool it would be to make lights blink, but on a city-wide basis. Haha, right? So they bought a bunch of these EFR devices on the used market and started hacking.
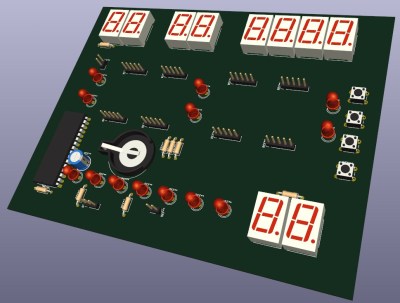
They did a lot of background digging, and found out that they could talk to the devices, both over their local built-in IR port, but also over radio. Ironically, one of the best sources of help they found in reversing the protocol was in the form of actually pressing F1 in the manufacturer’s configuration application – a program’s help page actually helped someone! They discovered that once they knew some particulars about how a node was addressed, they could turn on and off a device like a street lamp, which they demo with a toy on stage. So far, so cute.
But it turns out that these boxes are present on all sorts of power consumers and producers around central Europe, used to control and counteract regional imbalances to keep the electrical grid stable. Which is to say that with the same setup as they had, maybe multiplied to a network of a thousand transmitters, you could turn off enough power generation, and turn on enough load, to bring the entire power grid down to its knees. Needless to say, this is when they contacted both the manufacturer and the government.
The good news is that there’s a plan to transition to a better system that uses authenticated transmissions, and that plan has been underway since 2017. The bad news is that progress has been very slow, and in some cases stalled out completely. The pair view their work here as providing regulators with some extra incentive to help get this important infrastructure modernization back on the front burner. For instance, it turns out that large power plants shouldn’t be using these devices for control at all, and they estimate that fixing this oversight could take care of most of the threat with the least effort.
National power grids are complicated machines, to say the least, and the impact of a failure can be very serious. Just take a look at what happened in 2003 in the US northeast, for instance. And in the case of real grid failure, getting everything back online isn’t as simple a just turning the switches back on again. As [Fabian] and [Luca] point out here, it’s important to discover and disclose when legacy systems put the grid in potential danger.