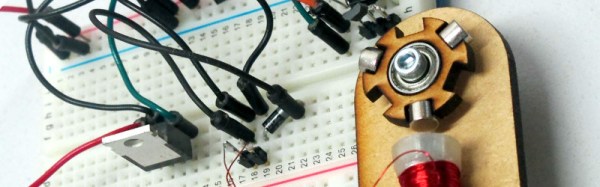
Sometimes there is no substitute for a real working model to tinker with when it comes to understanding how something works. Take a brushless motor for example. You may know how they work in principle, but what factors affect their operation and how do those factors interact? Inspired by some recent Hackaday posts on brushless motors, [Matt Venn] has built a simple breadboard motor designed for the curious to investigate these devices.
The rotor and motor bodies are laser-cut ply, and the rotor is designed to support multiple magnet configurations. There is only one solenoid, the position of which relative to the magnets on the rotor can be adjusted. The whole assembly is mounted on the edge of a breadboard, and can be rotated relative to the breadboard to vary the phase angle at which the drive circuit’s Hall-effect sensor is activated by the magnet. The drive circuit in turn can have its gain and time constants adjusted to study their effects on the motor’s running.
[Matt] has made all the design files available in his GitHub repository, and has recorded a comprehensive description of the motor’s operation in the YouTube video below the break. Continue reading “A Simple And Educational Brushless Motor”