The origin story for many who’d call themselves a member of the hacker community usually starts with taking things apart as a child just to see how they worked. For [Radoslav], that trend doesn’t seem to have slowed down, and he’s continued taking toys apart. Although since it’s his daughters little radio controlled car, he stuck to a non-destructive teardown. The result? He’s able to control the car with his laptop through a HackRF One SDR transceiver as shown in the video below the break.
[Radoslav] is no stranger to reverse engineering embedded devices, IoT gadgets, and probably more. So he started with what information was publicly available about the radio control interface in use. Many electronic devices sold in the US must be certified by the FCC (Federal Communications Commission) and prominently display their ID number, and this toy was no exception. The FCC database gave [Radoslav] enough information to know that the communication protocol is modulated with GFSK, a type of Frequency Shift Keying.
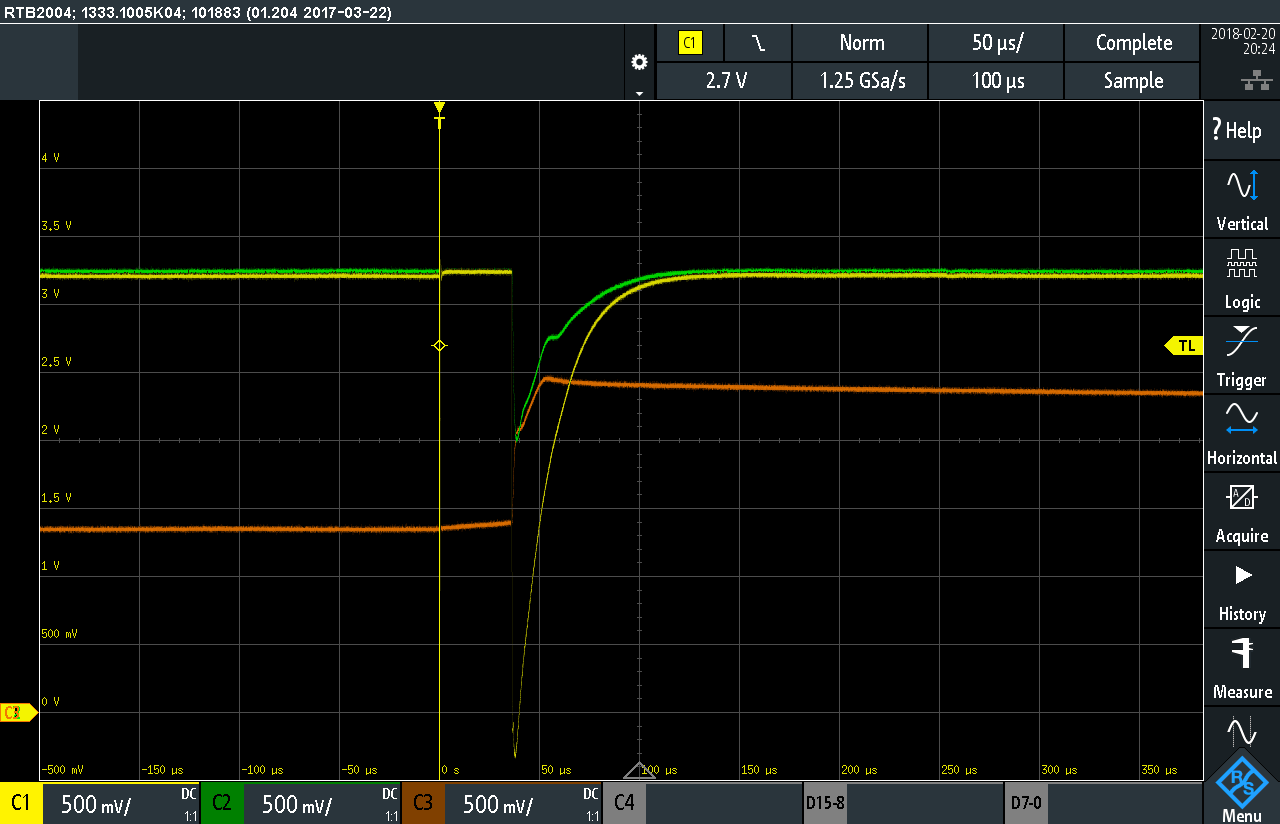
He fired up his favorite radio signal analysis tool and and got to work on the protocol itself. Along the way he found that communication between the car and controller is bidirectional but also very easy to get around. The result is that he can drive the car around with his laptop- definitely a cool hack, but for this one, the journey was surely the goal, not the destination.
If hacking on RC cars really gets your wheels turning, you might like this little RC car that can drive on the ceiling. Or if you’re feeling a bit hungry, check out how you can use the HackRF to nab a table at your local restaurant.