Nostalgia is a funny thing. If you experienced the early days of video games in the 1980s and 90s, there’s a good chance you remember those games looking a whole lot better than they actually did. But in reality, the difference between 2023’s Tears of the Kingdom and the original Legend of Zelda is so vast that it can be hard to reconcile the fact that they’re both in the same medium. Of course, that doesn’t mean change the way playing those old games actually makes you feel. If only there was some way to wave a magic wand and improve the graphics of those old titles…
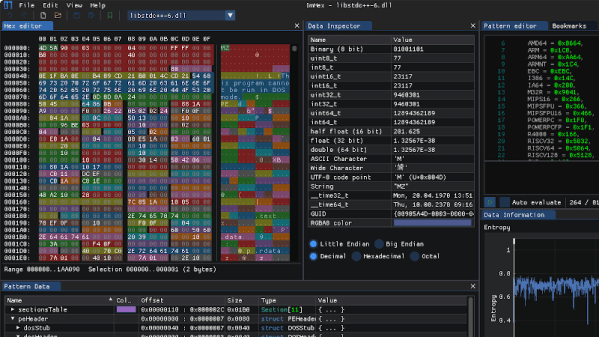
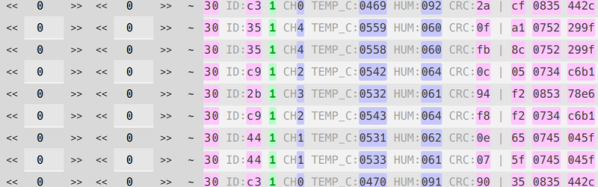
Well, if you consider Ghidra and a hex editor to be magic wands in our community, making that wish come true might be more realistic than you think. As [Alberto Marnetto] explains in a recent blog post, decompiling Stunt Island and poking around at the code allows one to improve the graphical detail level in the flight simulator by approximately 800%. In fact, it’s possible to go even higher, though at some point the game simply becomes unplayable.
Continue reading “Cranking Up The Detail In A Flight Simulator From 1992”