This year’s Digital Millennium Copyright Act (DMCA) triennial review (PDF, legalese) contained some great news. Particularly, breaking encryption in a product in order to repair it has been deemed legal, and a previous exemption for reverse engineering 3D printer firmware to use the filament of your choice has been broadened. The infosec community got some clarification on penetration testing, and video game librarians and archivists came away with a big win on server software for online games.
Moreover, the process to renew a previous exemption has been streamlined — one used to be required to reapply from scratch every three years and now an exemption will stand unless circumstances have changed significantly. These changes, along with recent rulings by the Supreme Court are signs that some of the worst excesses of the DMCA’s anti-circumvention clause are being walked back, twenty years after being enacted. We have to applaud these developments.
However, the new right to repair clause seems to be restricted to restoring the device in question to its original specifications; if you’d like to hack a new feature into something that you own, you’re still out of luck. And while this review was generally favorable of opening up technology to enable fair use, they didn’t approve Bunnie Huang’s petition to allow decryption of the encryption method used over HDMI cables, so building your own HDMI devices that display encrypted streams is still out. And the changes to the 3D printer filament exemption is a reminder of the patchwork nature of this whole affair: it still only applies to 3D printer filament and not other devices that attempt to enforce the use of proprietary feedstock. Wait, what?
Finally, the Library of Congress only has authority to decide which acts of reverse engineering constitute defeating anti-circumvention measures. This review does not address the tools and information necessary to do so. “Manufacture and provision of — or trafficking in — products and services designed for the purposes of circumvention…” are covered elsewhere in the code. So while you are now allowed decrypt your John Deere software to fix your tractor, it’s not yet clear that designing and selling an ECU-unlocking tool, or even e-mailing someone the decryption key, is legal.
Could we hope for more? Sure! But making laws in a country as large as the US is a balancing act among many different interests, and the Library of Congress’s ruling is laudably clear about how they reached their decisions. The ruling itself is worth a read if you want to dive in, but be prepared to be overwhelmed in apparent minutiae. Or save yourself a little time and read on — we’ve got the highlights from a hacker’s perspective.
Continue reading “DMCA Review: Big Win For Right To Repair, Zero For Right To Tinker” →
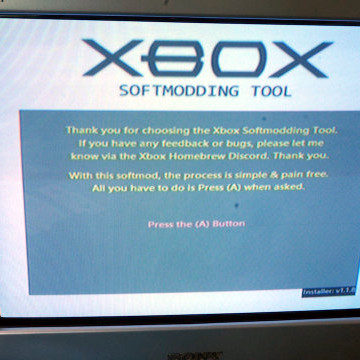 Don’t let that fool you into thinking the process requires nothing more than pressing a button; it’s actually quite involved, but more accessible now that [ezContents] has published a comprehensive walkthrough for softmodding an original Xbox, complete with loads of screenshots and photos.
Don’t let that fool you into thinking the process requires nothing more than pressing a button; it’s actually quite involved, but more accessible now that [ezContents] has published a comprehensive walkthrough for softmodding an original Xbox, complete with loads of screenshots and photos.